Business Email Compromise
I mentioned this in a previous post but we are seeing a large increase in phishing attacks from known sources. In other words, phishing attacks are coming from your friends, colleagues, and vendors. You trust these sources and you are likely to drop your guard more so than when say the Nigerian Prince email makes its way into your inbox. Obviously, if someone falls for the phish, this campaign lives on and that's how future attacks occur. But how does the original attack get legs underneath it? First, let's start with the phish and work our way backwards.
While this looks suspicious to me, the victim knows the account being used in this attack and they trust the source. In fact, the victim expects documents of this nature:
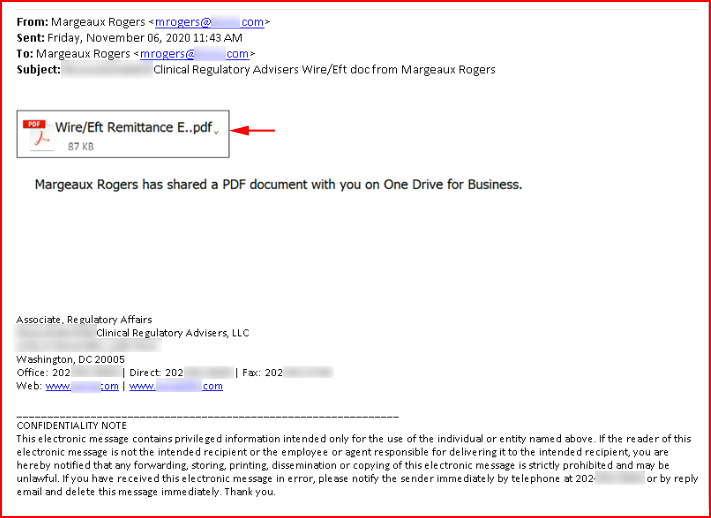
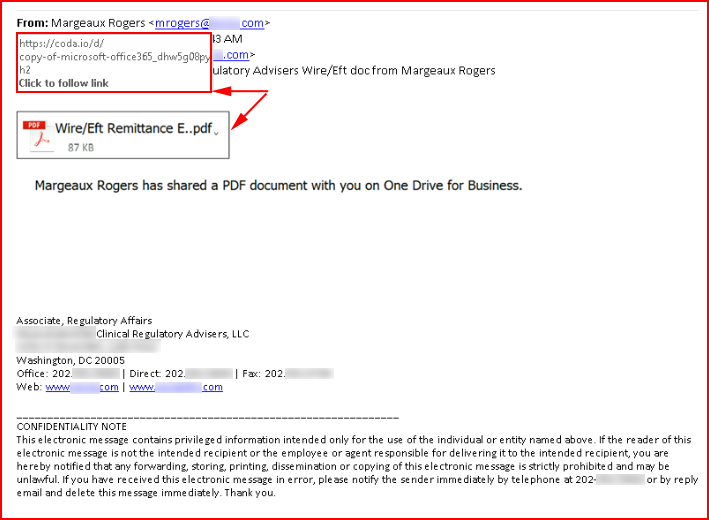
When we mouse over what appears to be an embedded document, we see that it's actually an image which points to coda.io etc. and it's starting to look even more suspicious:
Let's say this is victim0. How do we compromise victim0 to start this campaign? How about in breach data? I went digging through breach data for this company and I found quite a few accounts and passwords:
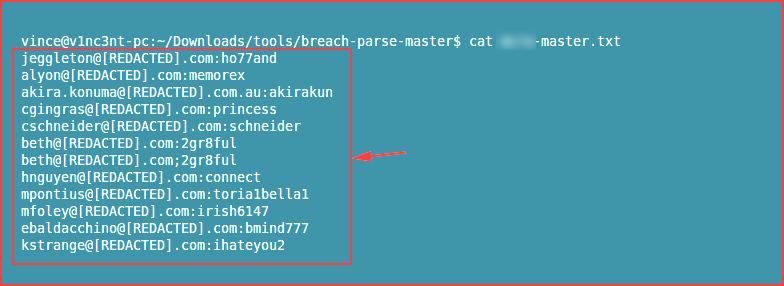
When I look at these passwords, I can tell they were not generated with a password manager and I would bet money that some of these (if not all of these) have been reused elsewhere. That's how it starts. A malicious attacker found an account, compromised it, and they were either able to take over an Office365 account, or they worked their way toward the Office365 account until they compromised it.
I guess technically, we don't know what mail provider they are using at this point but we can use nslookup to uncover that quickly.
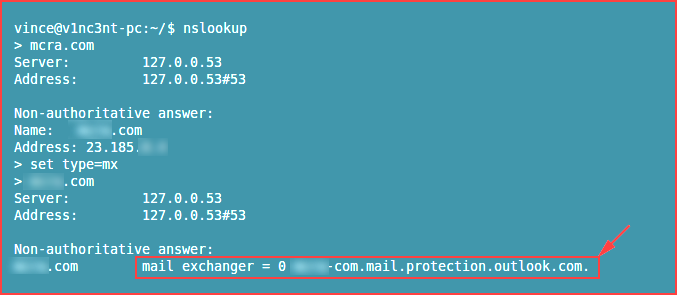
Ok, NOW we know they are using Office365.
Let's take this a step further. Using Hunter.io, we can gather more information about the company:
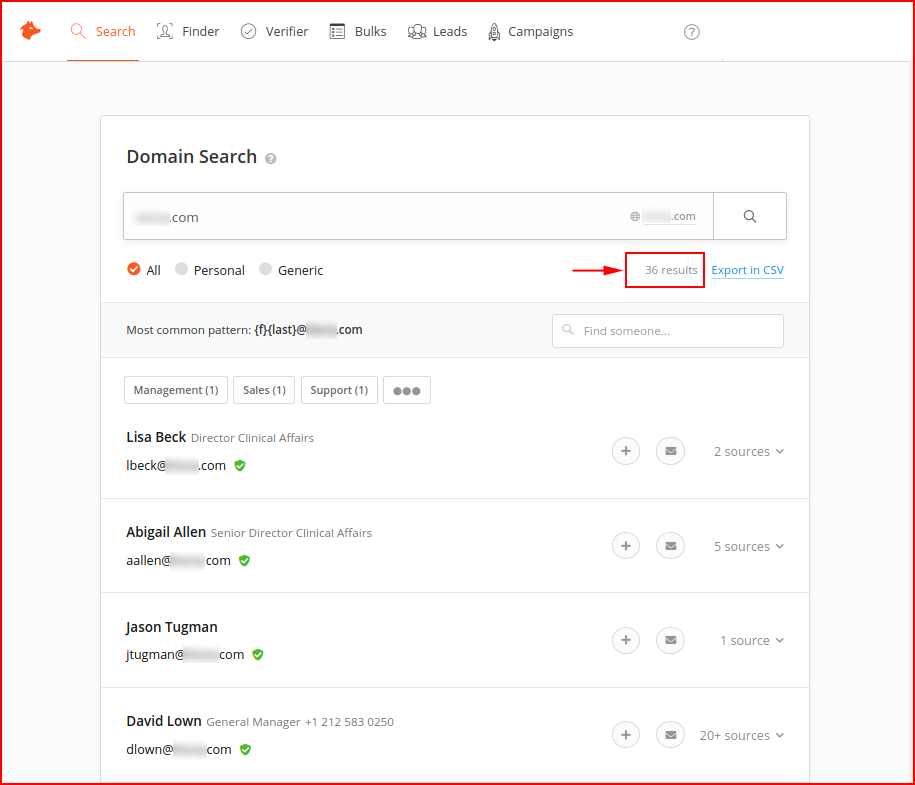
We decide to dig into the General Manager:
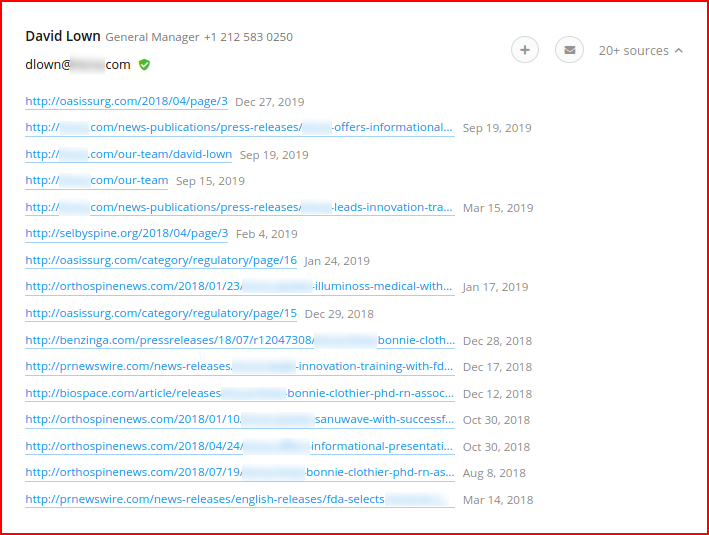
As we can see, there's a ton of information to be gathered from Hunter.io -- a FREE account, I would add. Obviously, this has gone to a more targeted approach but the point is that it didn't take but 5 minutes to dig up passwords, a mailing list, and specific information from the Hunter.io "sources" we can use in our campaign to hook a victim. That is one way for it to possibly start.
Prevention starts with unique passwords, phishing awareness training, and two factor authentication.
We need to educate users on what the latest attacks look like, how to identify phishing attacks, and how to report them. I've said this before, we can ALL be phished. So in those instances where we give up our credentials, two factor authentication is what's going to help stop the attacker from using our accounts for the next part of their campaign. In addition to the prevention mechanisms, we also need to be timely in the reporting aspect in case our defenses were also compromised. In my industry, people refer to users as the first line of defense. I think that's an incorrect statement. Users are not defenders. However, users can be a trip wire of sorts. When an attacker crosses the line, we want those users to make lots of noise so that the actual defenders can jump into action. That last part takes training as well since users are reluctant to report what they perceive as a mistake on their part.