CyberChef
When I spoke at BSides earlier this year, I met a guy who works for a company that provides SOC as a service. Our skills are not the same and if anything, he's on the receiving end of what I've create. I had a question about some of the obfuscation techniques I use -- specifically, I wanted to know how someone would approach the obfuscated code. He mentioned a tool -- CyberChef. I'd never heard of it and looking back, I don't know how I haven't heard of it. The description from their site states: "CyberChef - The Cyber Swiss Army Knife".
BSides was back in February but it was probably maybe a month or two ago that I started to dig into Cyber Chef's capabilities. Now I'm finding that I'm using it at least once per day to do something.
This is not a comprehensive walk through of the tool and honestly, you just have to start using it, poking around, and that's when you'll see its power. The ability to create "Recipes" which can be multiple iterations of multiple different processes is where I think this gets really useful.
Let's start with the basic UI: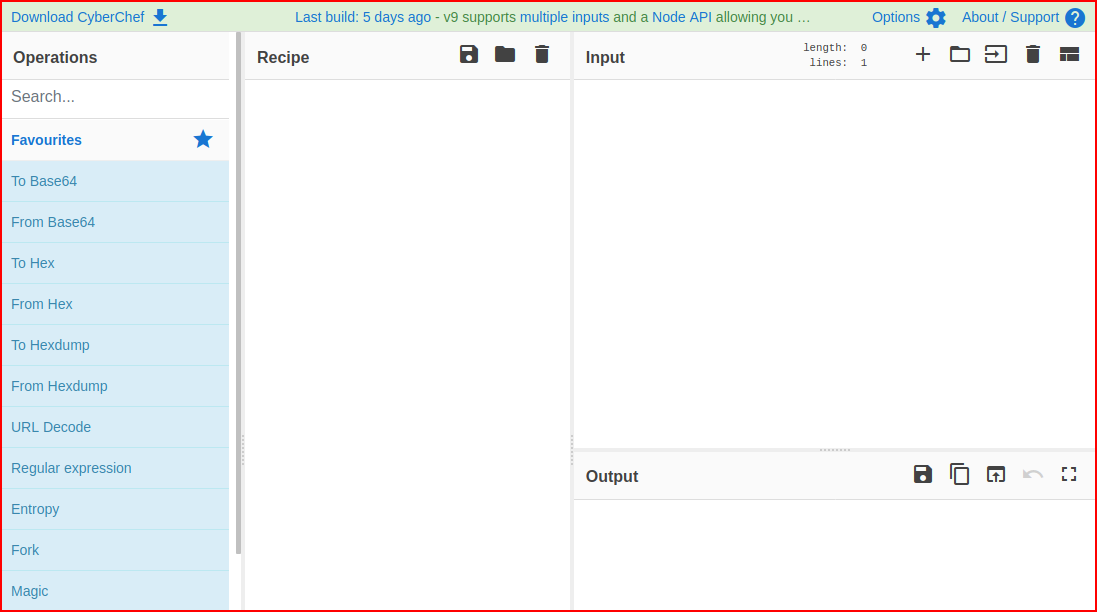
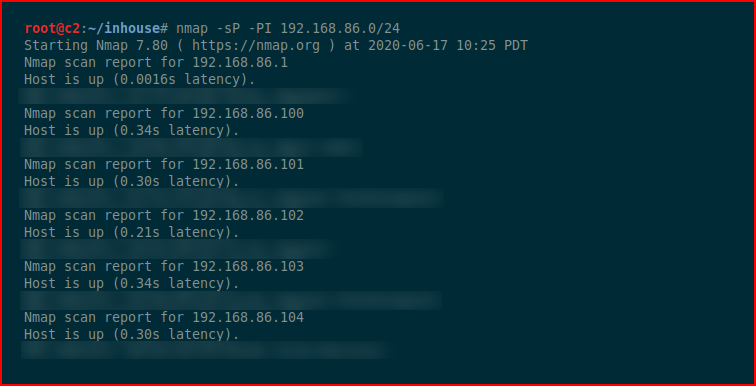
This is in no particular order but let's say I run a ping scan and I want to extract the IP addresses. And let's also pretend that I didn't know that this could do it:
nmap -sP -PI 192.168.86.0/24 | grep -E -o "([0-9]{1,3}[\.]){3}[0-9]{1,3}"
We get our output, copy it:
We paste it into the Input section of CyberChef, search for IP address, the recipe appears and:
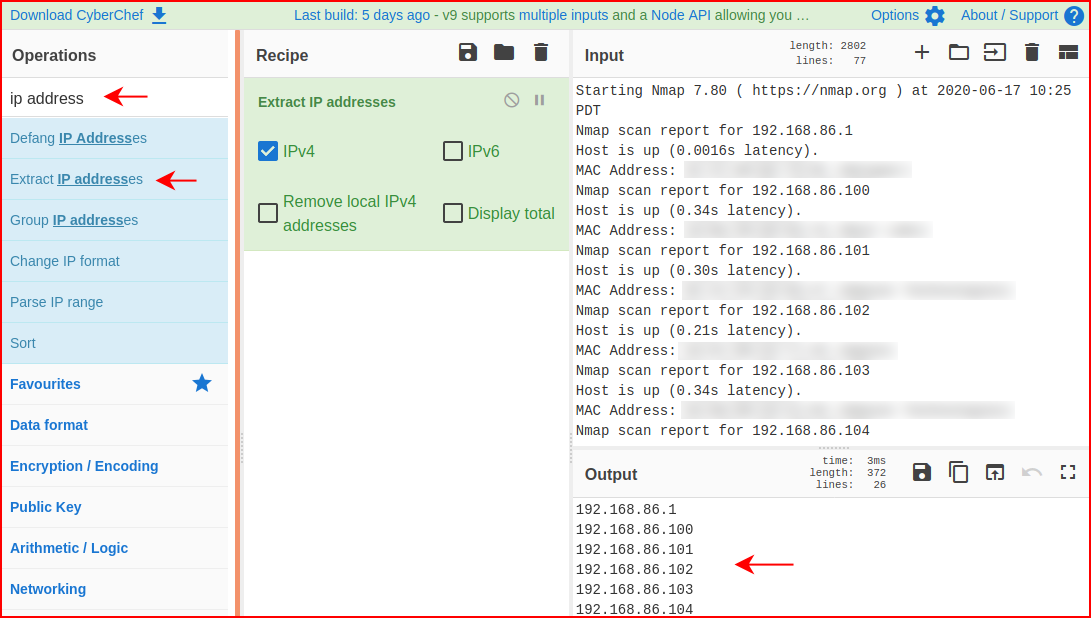
At the bottom, in the Output section, we find a clean list of IP's.
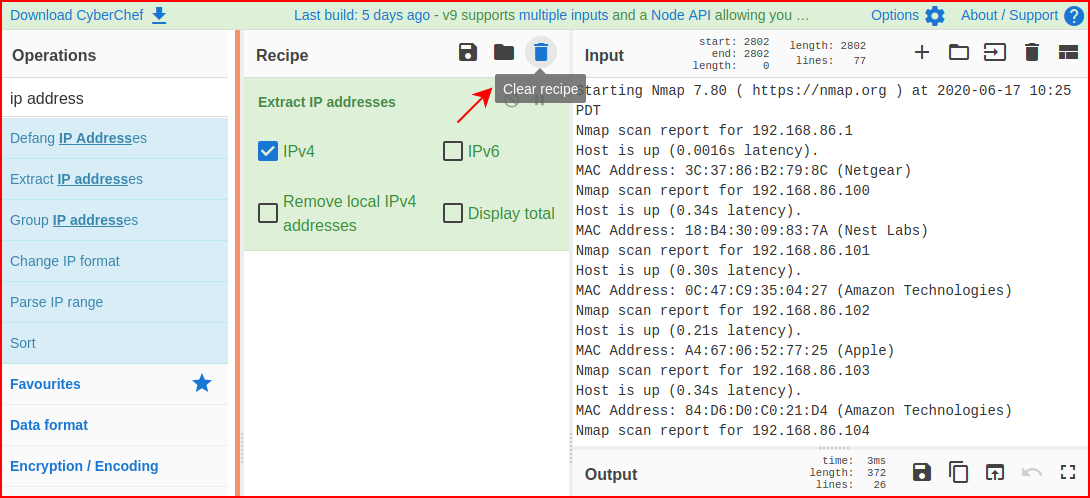
If we're done with this particular task and we're not going to chain items together, we should clear the recipe:
Let's say we've got some Base64 encoded text. Again, I realize we can decode this on the command line or in Burp Suite but we can decode from various encoders within CyberChef. So here we have our input:
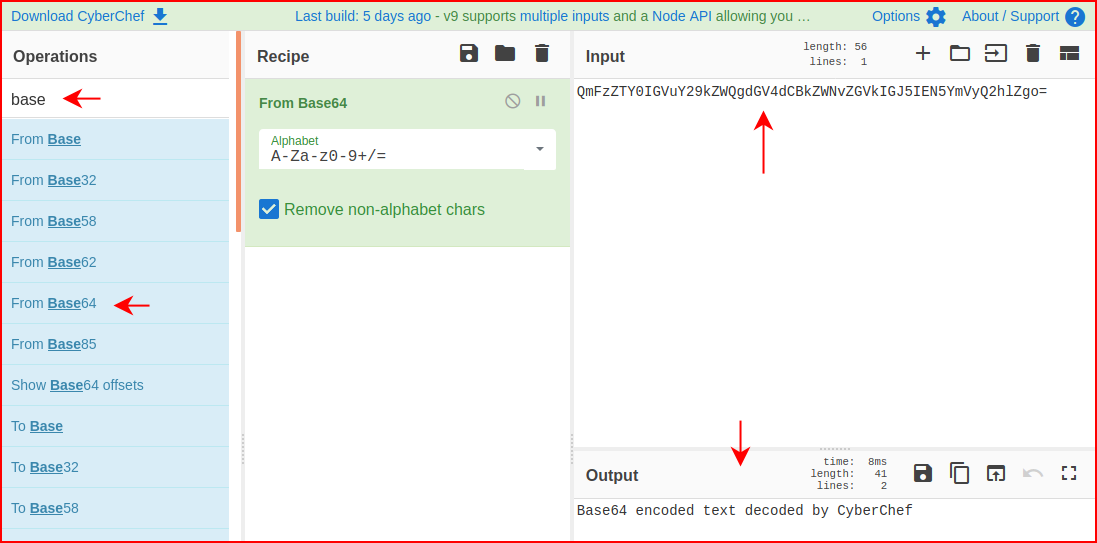
And we decode it for our output.
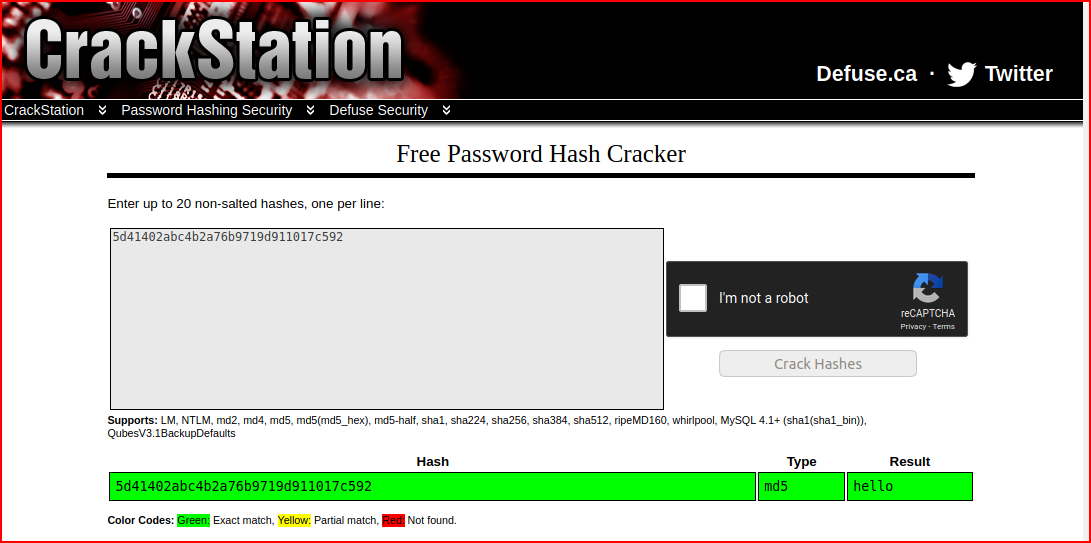
MD5 encoding:
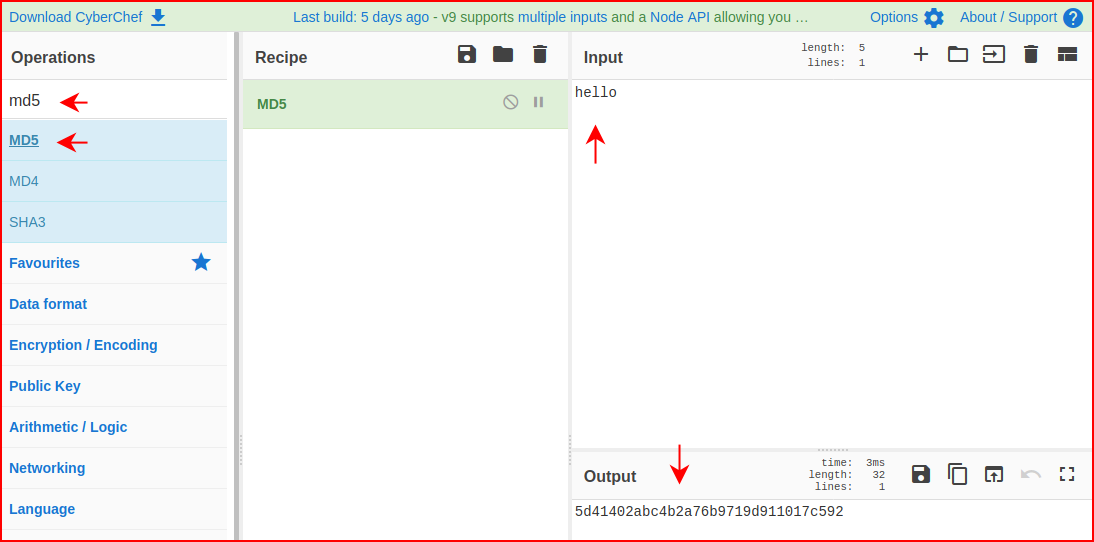
As a sanity check, we take it up to CrackStation:
How about Rot13?
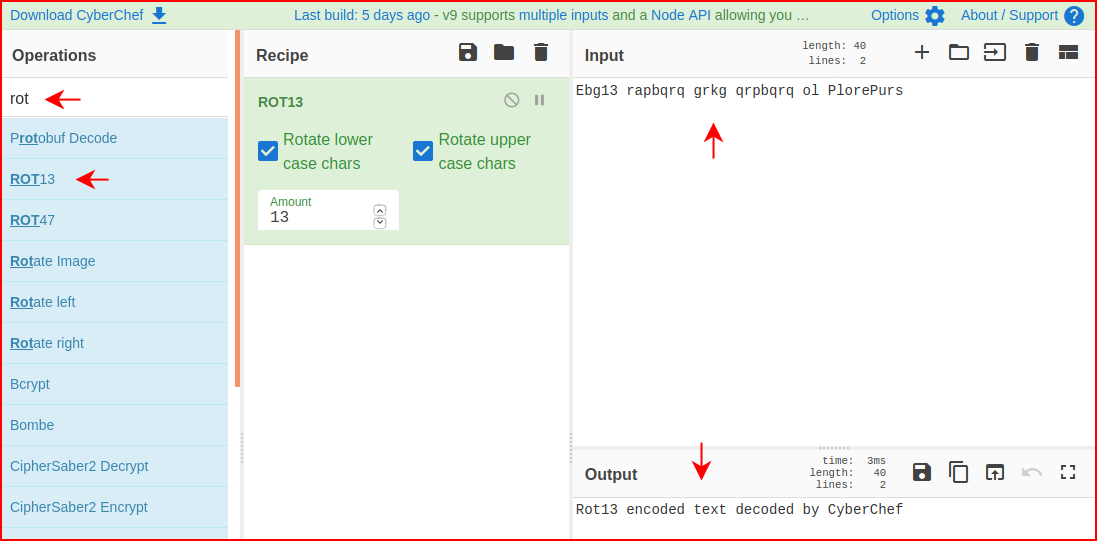
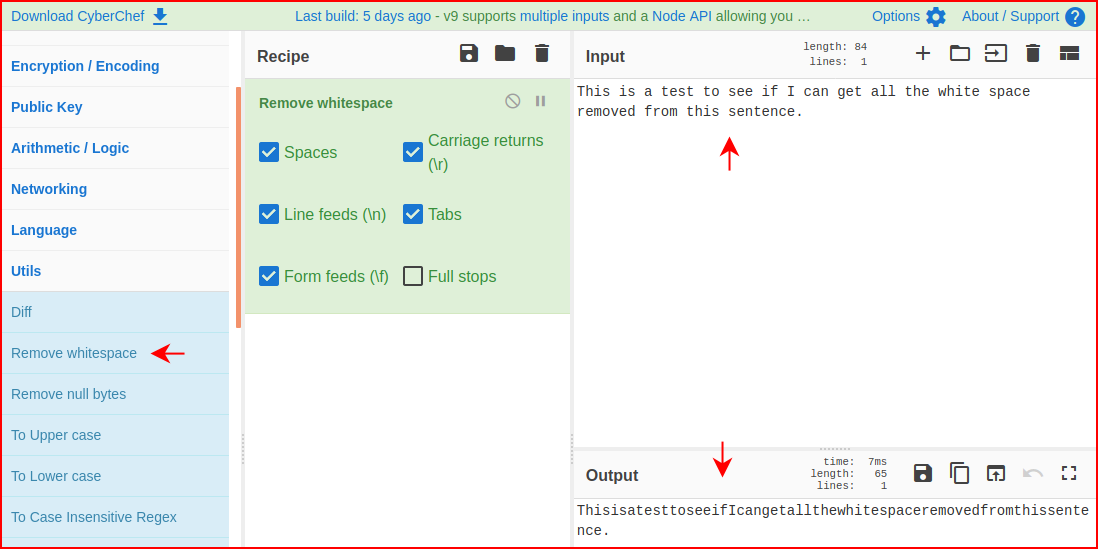
I literally used this yesterday when the output of a very long hash had line feeds:
Everything I've done here can be performed on a Linux command line but I don't always remember all of those commands.
There's so much more to it and I encourage you to look through the various tasks it can perform. I wish I'd learned of this tool prior to this year, it would have save me some time!