Pentbox Honeypot
If it seems like I'm on some sort of Wile E. Coyote quest to build the perfect booby trap, that is actually not the case despite how things look. Canaries, mazes, honeypots, there's definitely a recent theme and it's all related to a current project. The Pentbox honeypot doesn't actually fit my need but I saw it, downloaded it, and I thought it was an interesting idea. Pentbox is actually an enumeration toolkit of sorts but the honeypot feature is based off of a question -- what happens if someone tries to hack the penetration tester?
I think the assumption is that you need to have something watching your back when you're working and that's where the honepot feature comes into play. After playing around with it for a minute or two, the most obvious setup is that you pop open a tab, launch the honeypot, and just leave that tab open. Not to spoil but there's an advanced section where you can configure the system to beep on an alert.
I've set this up on clean install of Ubuntu 18.04 so there are a couple of steps to get this running:sudo apt install ruby-fullgit clone https://www.github.com/technicaldada/pentboxcd pentboxtar -xf pentbox.tar.gzcd pentbox-1.8sudo su./pentbox.rb
Installing Ruby: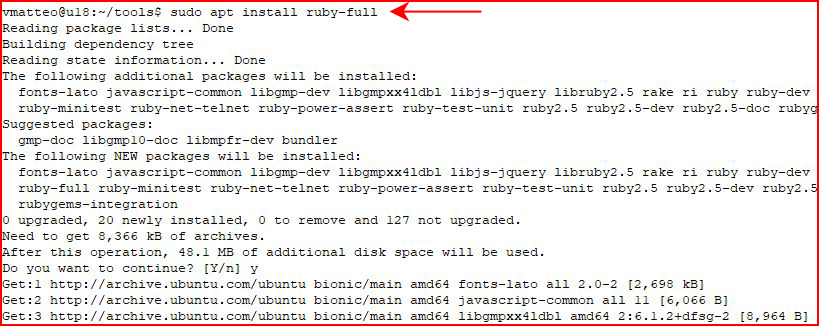
Grabbing Pentbox:
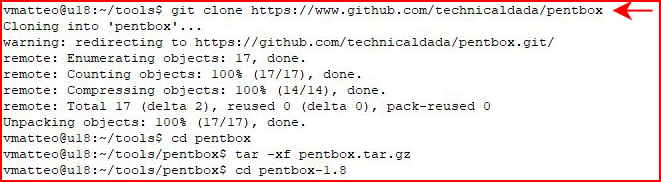
After we extract and move into the working directory, we need to execute as root.
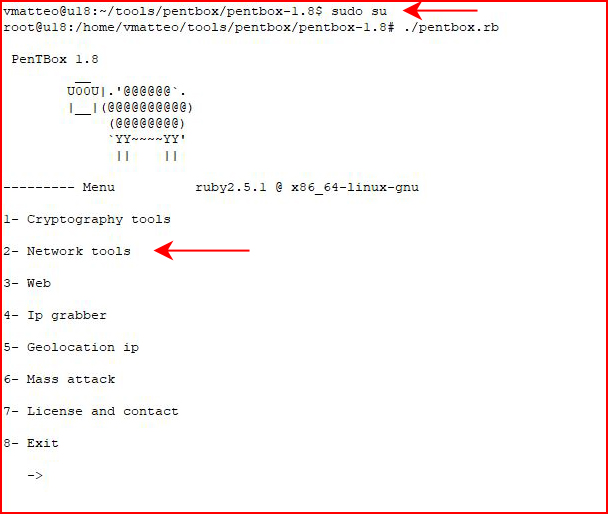
From the main menu, we choose Network tools:
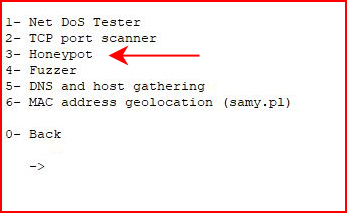
We choose Honeypot:
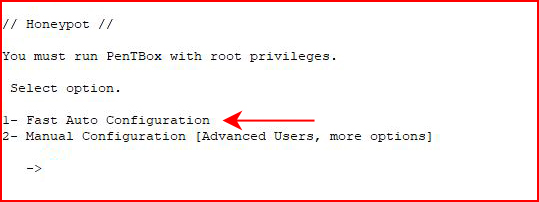
For a quick setup, go with Option #1:
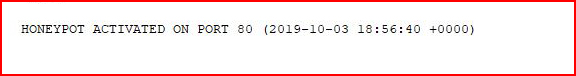
And then we wait:
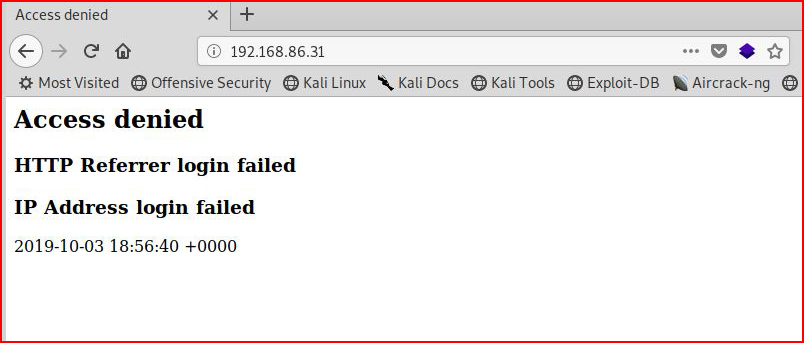
When we browse from our attacking machine, we see:
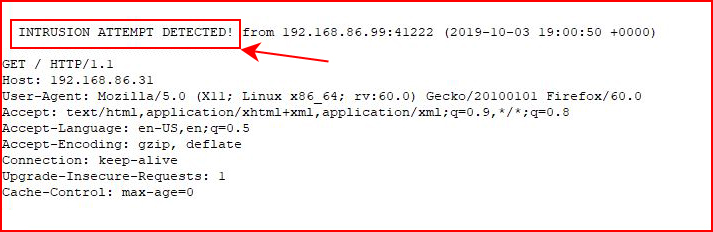
And back on our honeypot, we see the alert:
Back to our options screen, if we choose Option #2:
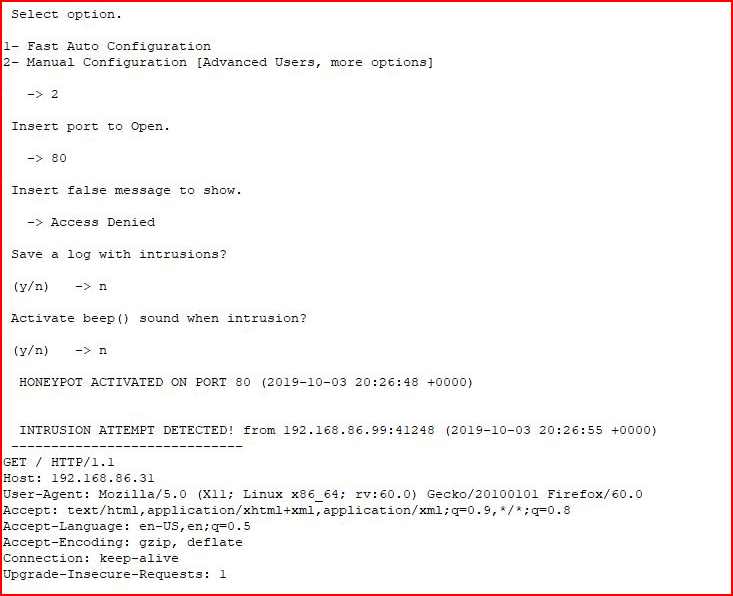
We have a few configuration options and the most obvious change is the message the attacker sees:
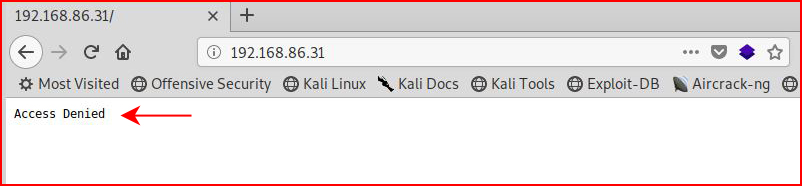
Keep it generic and give as little information about the honeypot as possible. If you open up netcat to the honeypot, you don't get anything useful but it does appear suspicious.
Anyway, aside from that, I checked out a few of the tools. Not my thing but the honeypot aspect is a cool idea.