HttpOnly
If it hasn't been obvious from my latest round of posts, I've been trying to improve my bug hunting skills. Essentially, I've been finding applications with recently disclosed vulnerabilities, installing the current version, and then hunting for more vulnerabilities. My thinking is that if there's one recent bug, there are probably more. At the very least, I should be able to find a cross site scripting vulnerability (XSS).
XSS is the equivalent of hacker graffiti but if you can steal the session cookie, you can possibly turn that into session hijacking and / or cross site request forgery (CSRF). That makes things a little more interesting than just an alert message.
I saw a recently vulnerability discovered in Kimai which is a time tracking application. I fired up Kimai on a server and I started to poke around.
We start off with creating a customer: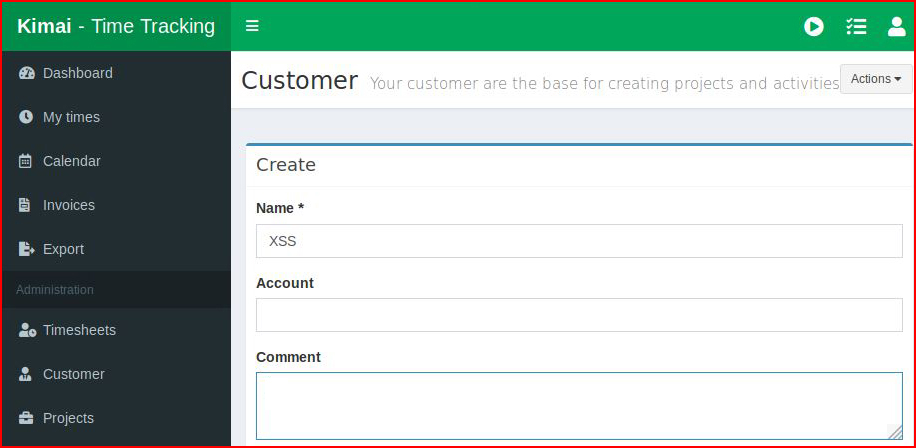
In the comment field, we insert our XSS: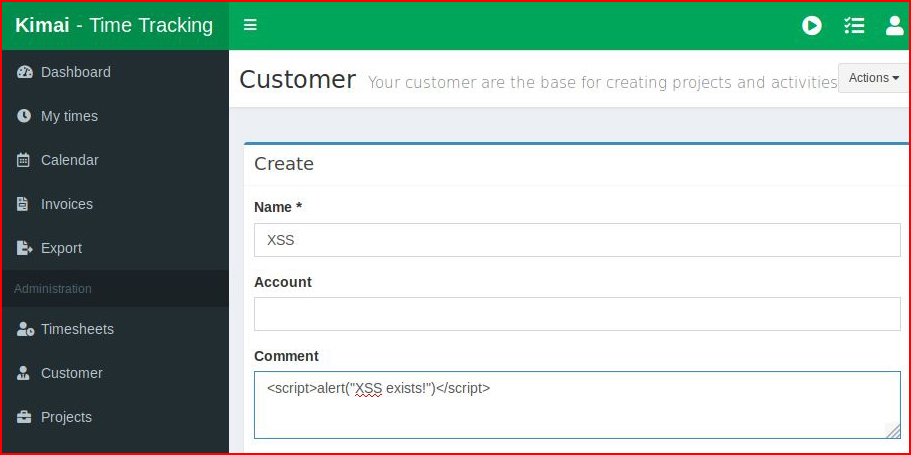
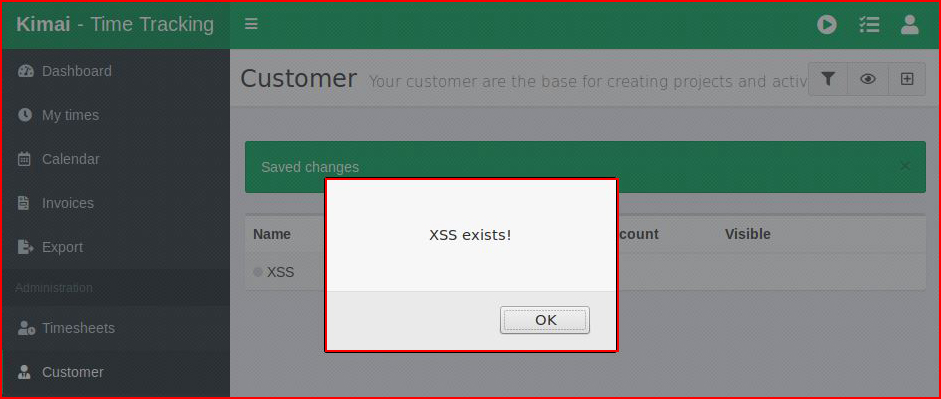
When we create the customer, we see:
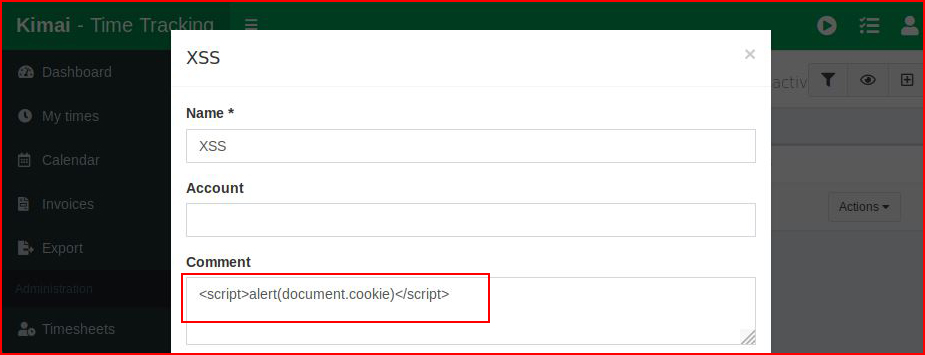
So far so good. Now we attempt to view the session cookie:
When hit submit:
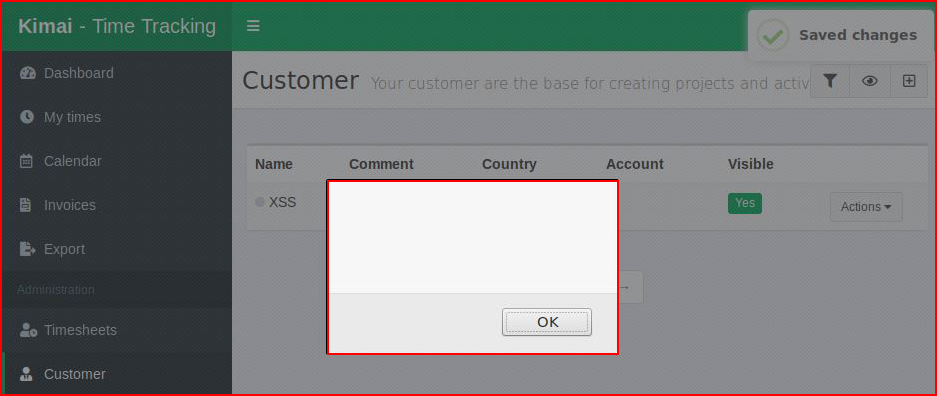
NOTHING.
When we inspect the page, wee find: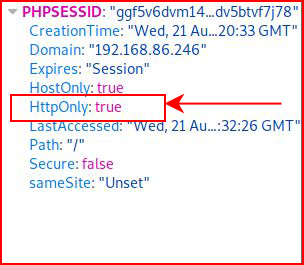
On production servers, this would be accurate because we set this in the apache2.conf file with:Header edit Set-Cookie ^(.*)$ $1;HttpOnly;Secure
But this isn't a production server and I'm confused as to where this is coming from. After some hunting, I find this: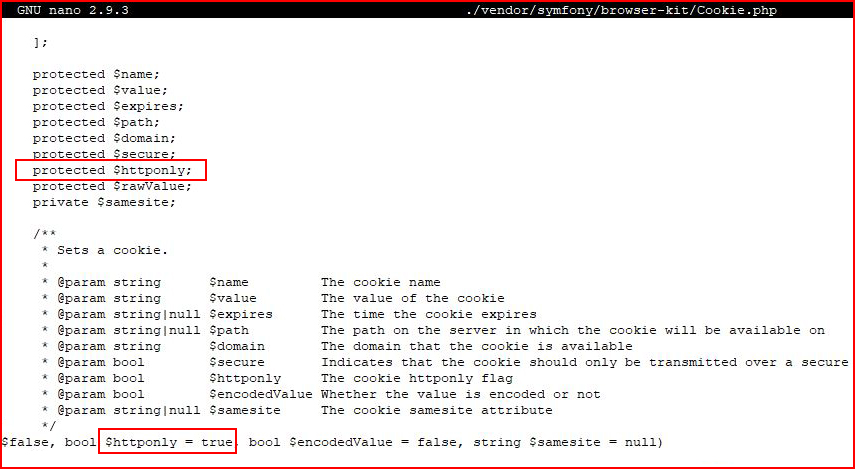
I do some digging around on the web and I find that this is part of the "Symfony Framework : The leading PHP framework to create websites and web applications."
And as you can see from above, there's security baked into the application. Pretty cool, honestly. But it's going to make my job harder. I'm not done poking around but I think I'm going to get shut down.